Docker has revolutionized how purposes are developed and delivered by enhancing the effectivity and scaling of containerization. Nevertheless, the fast proliferation and extensive adoption of Docker expertise has elevated numerous critical safety vulnerabilities. The gadgets beneath enumerate some key approaches in direction of optimum safety in Docker containers.
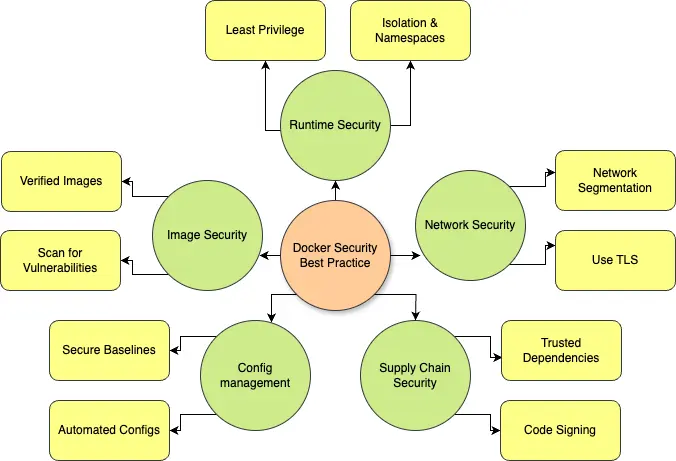
Key safety areas in Docker
Picture safety:
Base photos are the inspiration of Docker containers, and making certain their integrity is paramount. When organizations use untrusted or outdated photos, they threat introducing potential vulnerabilities into their containers, which can result in extreme safety exposures.
To successfully mitigate this threat, organizations ought to use solely verified photos from trusted sources and make it routine to scan these photos for any vulnerabilities which will exist often. The most effective practices on this regard embody implementing multi-stage builds, which assist reduce the assault surfaces that is perhaps exploited, in addition to making certain that the pictures are stored updated with the most recent safety patches accessible.
Runtime safety:
Poorly configured containers can turn out to be uncovered to completely different runtime threats and vulnerabilities. It’s important to run containers with the minimal privileges they should carry out their roles, and this may be considerably facilitated by working them in namespaces mixed with management teams for isolation, which is able to assist to forestall privilege escalation and potential container escapes.
Apart from, real-time monitoring of what occurs inside a container is extremely required for on-time detection and correct response to safety incidents earlier than they’ll turn into extra extreme points.
Community safety:
With out correct community segmentation, lateral motion can shortly happen with attackers inside containerized environments, creating a big safety threat. The dearth of acceptable community segmentation means enough community segmentation practices and strict insurance policies have to be carried out and adhered to, whereas encryption with TLS is required to maneuver knowledge securely.
It’s additionally critically vital to actively monitor and log all flows to detect unauthorized entry makes an attempt and stop potential breaches earlier than they trigger critical hurt.
Configuration administration:
Misconfigurations are among the many most vital contributing components to vulnerabilities inside container environments. If this situation is to be addressed sufficiently, organizations should change their methods and solely rely partially on configurations offered by Docker within the default occasion.
As a substitute, safe custom-configured baselines for container deployments ought to be developed and created. As well as, adopting automated configuration administration mixed with Infrastructure as Code (IaC) practices ensures consistency and safety when implementing a number of operational environments.
Provide chain safety:
Containers normally depend on third-party libraries, which can introduce vulnerabilities when the versioning isn’t vetted. To safe the container provide chain, a stable technique for dependency administration, implementation of code signing for verification, and well timed part updates to keep away from dangers brought on by outdated dependencies are important.
Conclusion
Whereas Docker scales up and deploys nearly any software, you’ll be able to’t neglect its safety. By following these practices — securing base photos so they’re freed from vulnerabilities, making use of the precept of least privilege to attenuate entry rights, enhancing community defenses to guard knowledge in transit, automating configuration administration to cut back human error and, most significantly, defending the availability chain to not introduce threat — organizations can successfully construct a resilient and safe containerized infrastructure that meets their wants.
With these measures, Docker environments can keep agile, scalable, and well-protected from varied quickly evolving fashionable threats.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share:
