The Black Hat Community Operations Heart (NOC) gives a high-security, high-availability community in probably the most demanding environments on the earth: the Black Hat occasion.
The NOC companions are chosen by Black Hat, with Arista, Cisco, Corelight, Lumen, NetWitness and Palo Alto Networks delivering from Las Vegas this yr. Cisco is the official Area Identify Service, Malware Evaluation and Cellular Machine Administration supplier. The Meraki workforce is writing a weblog concerning the experiences in defending and managing the Black Hat cellular units.
The companions additionally present built-in safety, visibility and automation: a Safety Operations Heart (SOC) contained in the NOC, with Grifter ‘Niel Wyler’ and Bart Stump because the leaders.

Integration is essential to success within the SOC of the NOC. At every convention, now we have a hack-a-thon to create, show, take a look at, enhance and eventually put into manufacturing new or improved integrations. To be a NOC accomplice, you have to be prepared to collaborate, share Automated Programming Interface (API) keys and documentation, and are available collectively (at the same time as market opponents) to safe the convention for the nice of the attendees.
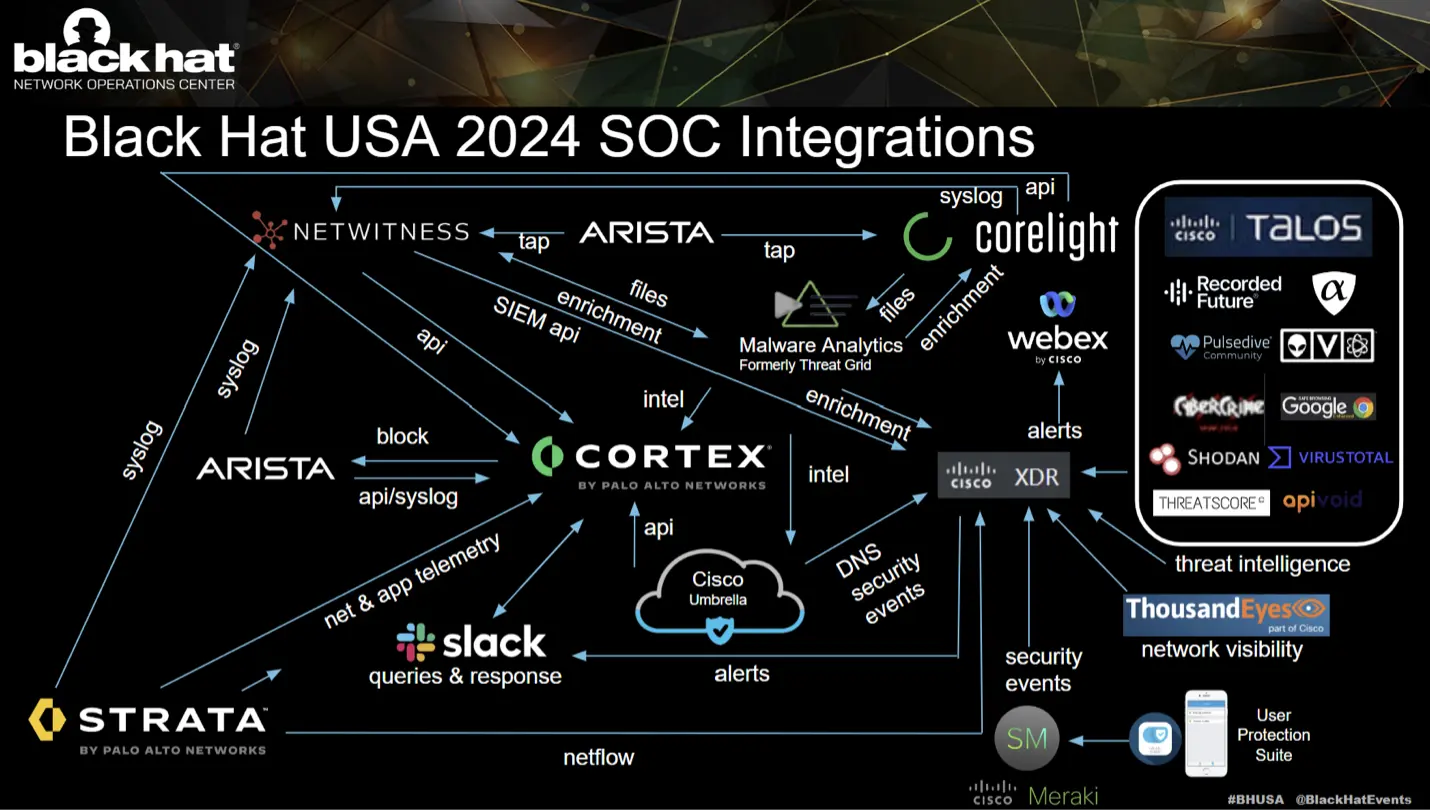
XDR integrations
Cisco joined the Black Hat NOC in 2016, when requested to supply automated malware evaluation with Risk Grid. The Cisco contributions to the community and safety operations developed, with the wants of the client, to incorporate extra parts of the Cisco Safety Cloud:
The NOC leaders allowed Cisco (and the opposite NOC companions) to usher in extra software program to make our inside work extra environment friendly and have larger visibility. Nonetheless, Cisco just isn’t the official supplier for Prolonged Detection & Response (XDR), Community Detection & Response or Collaboration.
- Cisco XDR: Community Site visitors Visibility and Risk Detection/Risk Looking/Risk Intelligence Enrichment/Government Dashboards/Automation
- Cisco Webex: Incident notification and workforce collaboration
The Cisco XDR command heart dashboard tiles made it straightforward to see the standing of every of the related Cisco Safety applied sciences, the general risk panorama and the standing of community availability as monitored by ThousandEyes brokers.
Under are the Cisco XDR integrations for Black Hat USA, empowering analysts to analyze Indicators of Compromise (IOC) in a short time, with one search. We respect alphaMountain.ai, Pulsedive and Recorded Future donating full licenses to the Black Hat USA 2024 NOC. Additionally, take a look at the weblog on XDR turning one yr previous and the affect of Black Hat occasions.
One of many new integrations this yr was with a utility written by considered one of our SOC workforce members. Each safety skilled — particularly SOC analysts and responders — have a collection of “fast lookup” type instruments that they use to reply varied questions on artifacts in an investigation. Shodan is a superb instance; “given an IP handle, what providers is that IP offering, and what software program are they utilizing to supply it?”. Paste the IP into Shodan, and you’ll probably get your reply. With the Shodan integration in XDR, you don’t even have to repeat and paste — simply click on the IP after which within the drop down menu, click on the Shodan hyperlink. However there are a whole bunch of such instruments…
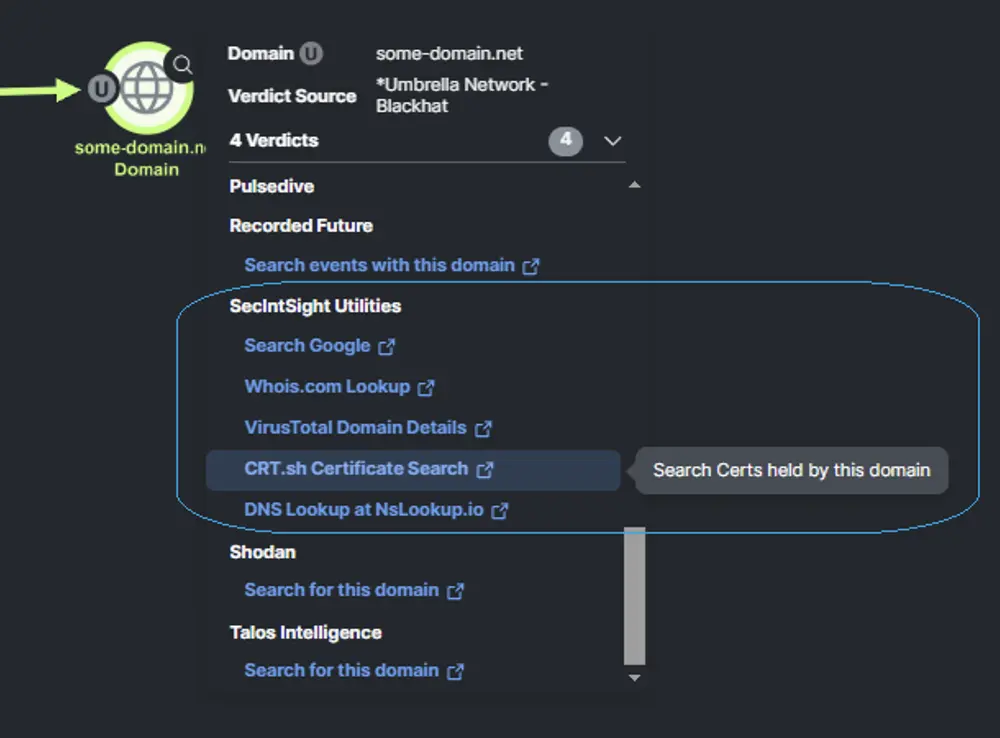
Ben took one of many integration server templates that Cisco Safety revealed on Github and modified it to our wants. He then hosted it on his cloud supplier of selection, added it to our XDR configuration and will add these easy pivots to XDR on the fly. A easy edit of a textual content file on the server and we may soar from any observable to any new related reference website that anybody had steered.
Cisco XDR is constructed on the beliefs of an open integration framework, with revealed knowledge fashions, API specs and pattern code accessible to be modified or used as examples/tutorials (together with precise tutorials at DevNet). This dedication to extensibility permits for modifications such because the above with out requiring any motion from the XDR growth or product groups, permitting clients to tailor XDR to their distinctive wants.
For instance, an IP tried <AndroxGh0st> Scanning Site visitors towards the Registration Server, blocked by the Palo Alto Networks firewall.
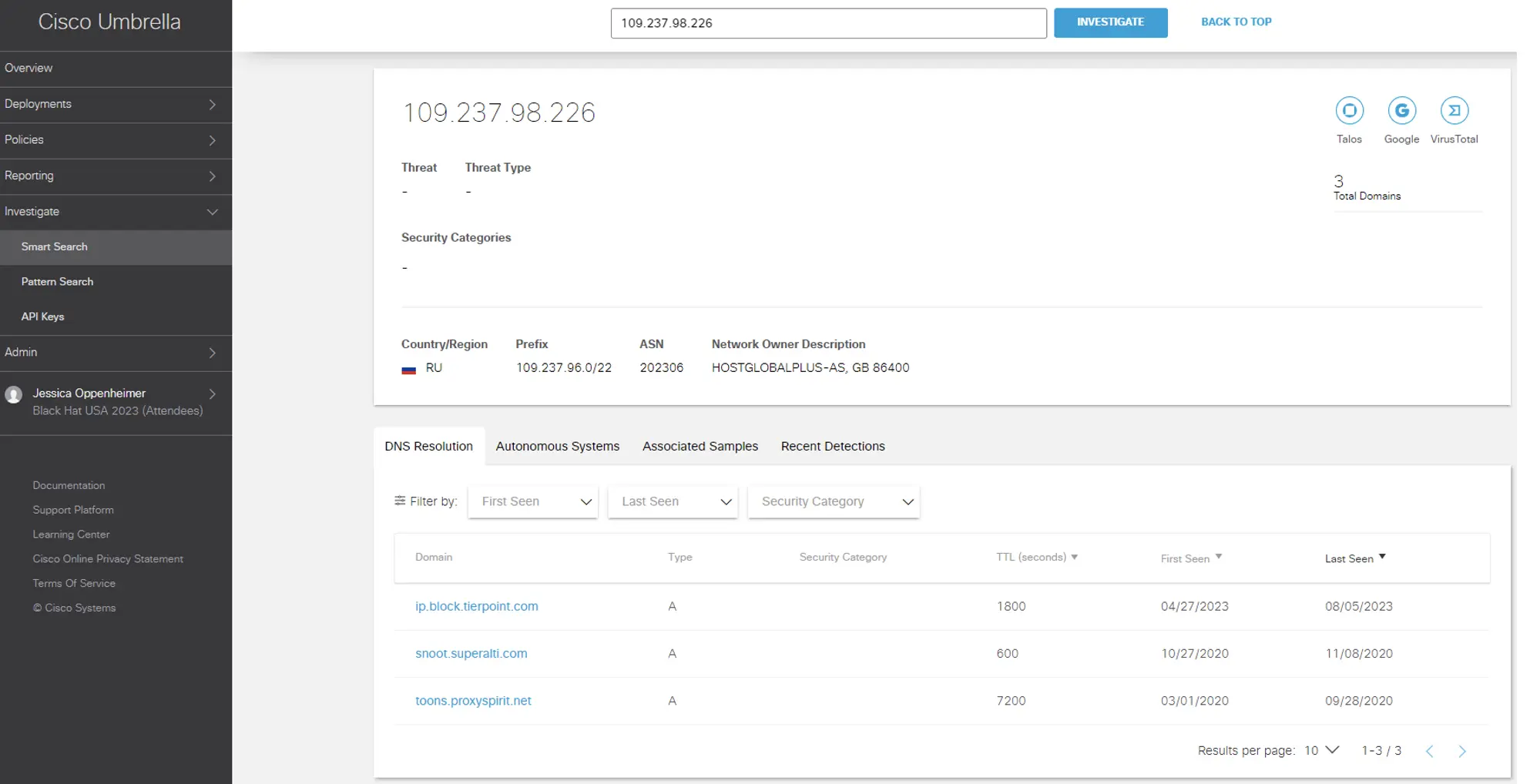
Investigation of the IP confirmed: It was identified malicious.
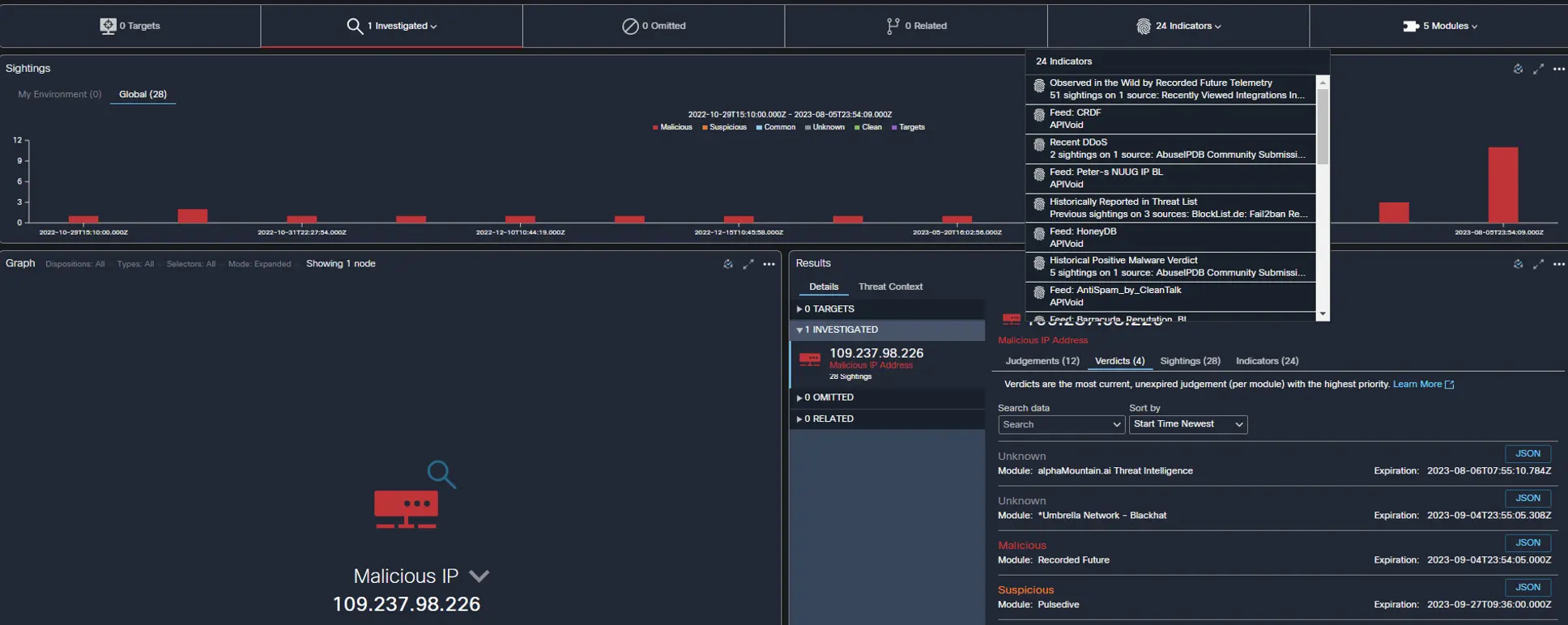
Additionally, the geo location is in RU and identified affiliated domains. With this data, the NOC management accepted the shunning of the IP.
XDR: Asset visibility
By: Ben Greenbaum
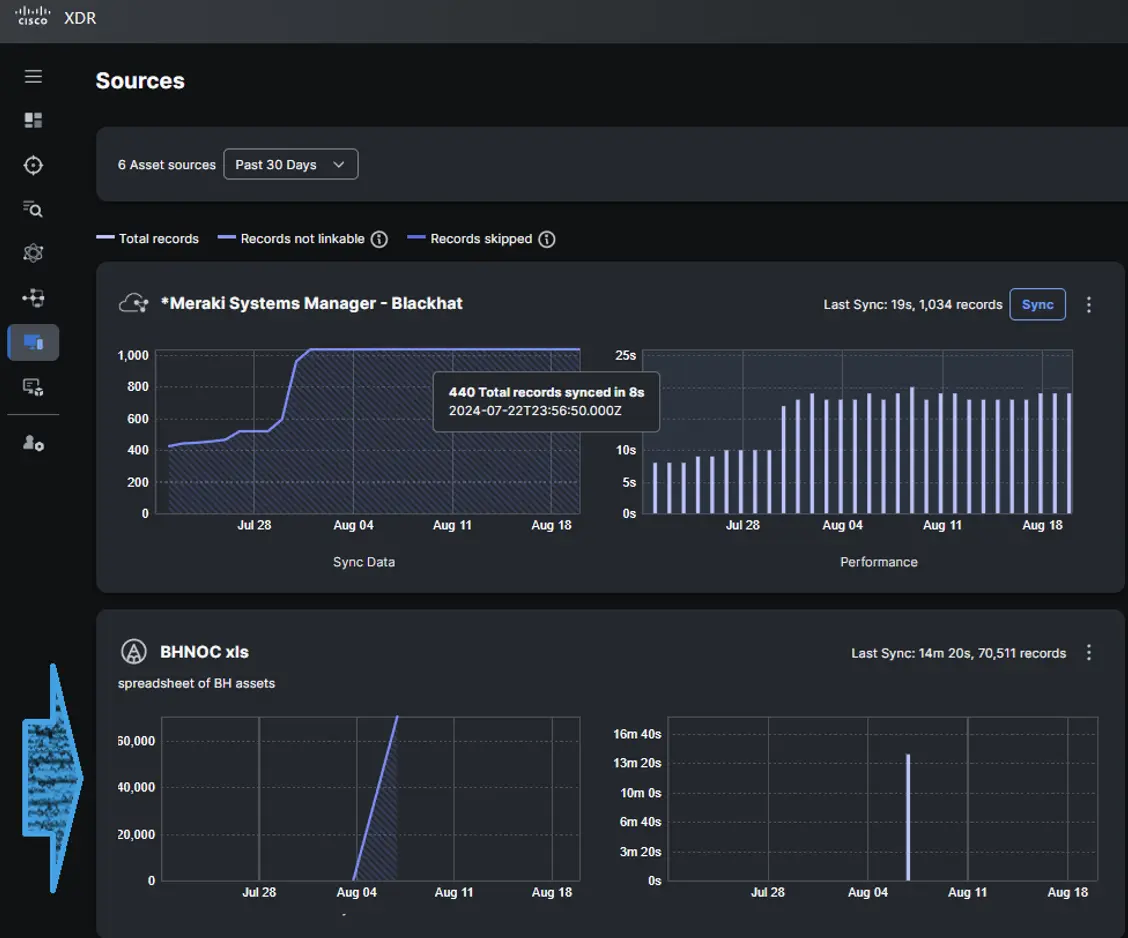
Because the Black Hat community evolves, completely different distributors are given alternatives to convey their merchandise into the toolbox. On account of this ongoing biking, we didn’t have entry to the depth of intelligence beforehand offered by deployment of a Meraki wi-fi infrastructure. Nonetheless, because of the functionality constructed into XDR Asset Insights to add a customized CSV file of belongings, we had been capable of simply operationalize identified community topography into investigative and response operations.
One of many distinctive challenges of the Black Hat surroundings is how completely different it’s from a “regular” buyer’s manufacturing community. We’ve a couple of hundred units whose safety is our major purpose, however tens of 1000’s of unmanaged (and sometimes hostile) units within the native community which we need to shield from one another and shield the skin world from. This distinctive association very a lot drives residence the worth that an EDR brings to an XDR resolution. With out good endpoint visibility, the problem is way larger. The advantage of an open XDR method that isn’t an evolution of an current EDR providing is that it may be considered one of a number of EDRs, however “one” is preferable to none.
Malware Analytics
By: Ben Greenbaum
Cisco Malware Analytics (previously Risk Grid) was once more used because the backend file evaluation and malware detection engine. We supported our companions from CoreLight and Netwitness, with evaluation of information pulled from clear textual content (convention attendee) and choose encrypted classes (important infrastructure).
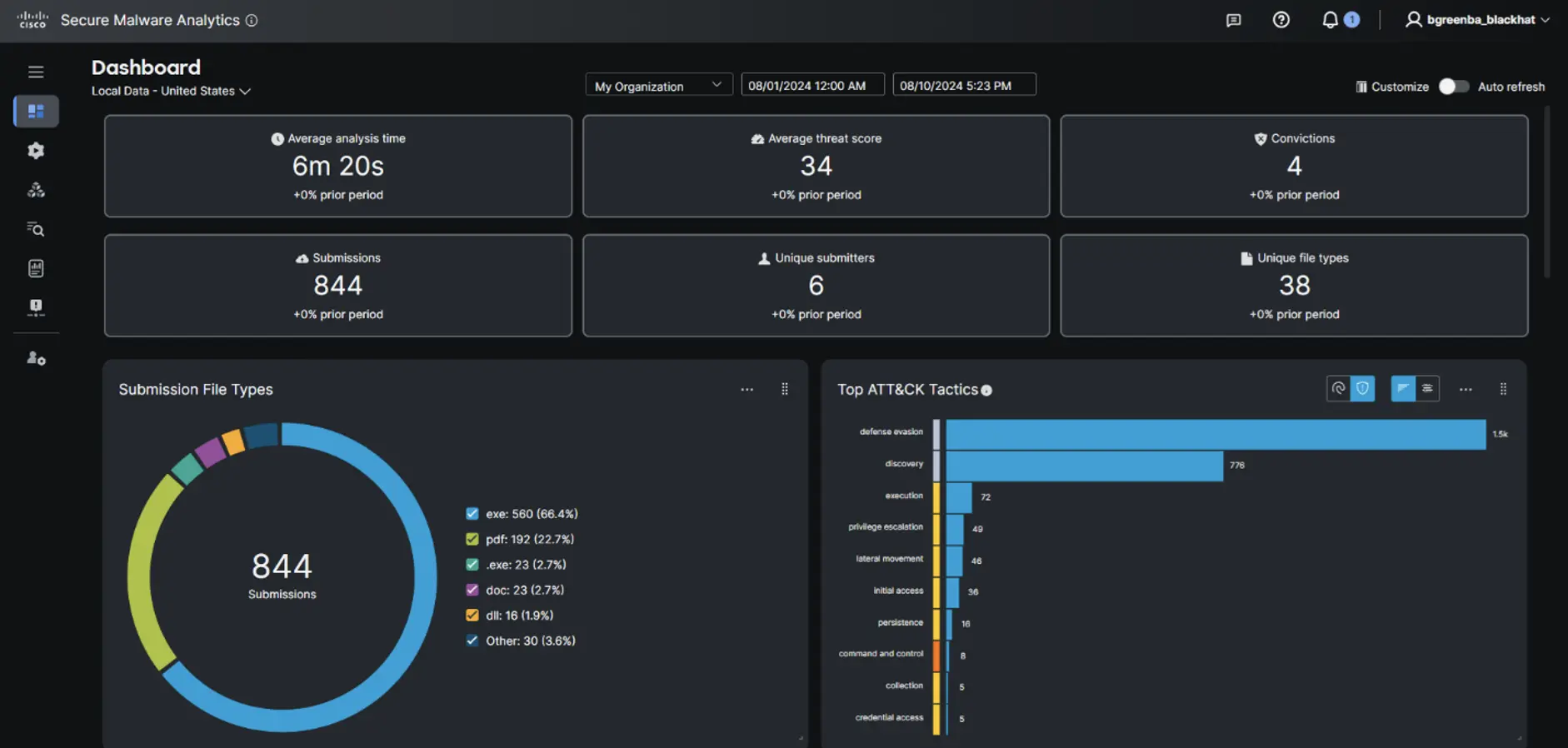
As common, the information present in clear textual content communications had been a superb indicator of what sorts of knowledge could be anticipated to be leaked by a crowd of safety professionals, and this yr the end result rated a strong “much less terrible.” Doubtlessly spicy content material included varied PII (names, employers, positions, electronic mail addresses, and many others.) from Black Hat receipts and some company electronic mail attachments.
And whereas Umbrella did alert us to some wandering infections phoning residence, we will say that not less than no malware was transferred…within the clear.
By: Aditya Sankar
Cisco XDR features a built-in automation functionality referred to as XDR automation. If in case you have heard of Safety Orchestration Automation Response (SOAR), Cisco XDR has the total suite of SOAR options. That features the flexibility to drag-and-drop prebuilt code blocks in a selected sequence to create a customized workflow, executing arbitrary API calls to function one-click response actions and creating guidelines to set off workflows primarily based off a schedule or another standards.
We’ve been utilizing XDR Automate at Black Hat for 3 years to enhance the Cisco providers to our joint buyer, Black Hat, and have carried out a wide range of use circumstances. Nonetheless, this has usually required fairly a little bit of time to study APIs and create a very customized workflow. With the most recent XDR Automation Trade, the Trade web page is used to search out, view, set up and uninstall pre-written workflows which were launched or accepted by Cisco engineers and content material suppliers. Workflows authored by the group have handed a primary high quality test and are supported by the Cisco DevNet Neighborhood on a best-effort foundation. The Exchanges helps allow collaboration between workflow creators and moreover reduces the time it takes for a person to expertise worth from XDR automation.
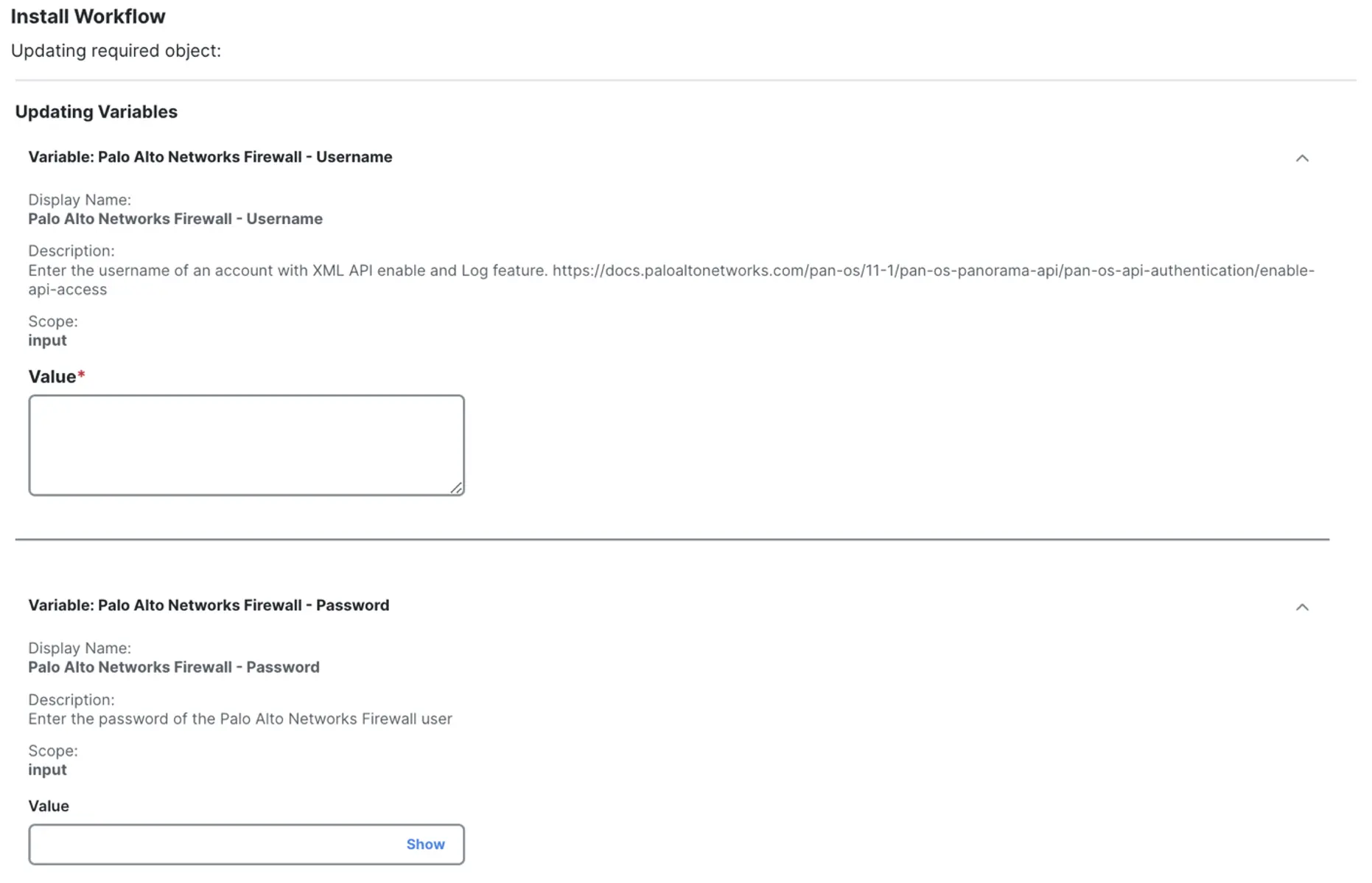
Shout out to Ivan Berlinson, who wrote a workflow to drag risk logs from the Palo Alto Networks API and create Incidents in Cisco XDR. Since Ivan was variety sufficient to publish the workflow to the Trade, it was extraordinarily straightforward to import the workflow and get it operational. Putting in a workflow from the trade is actually like strolling by means of a configuration wizard. It features a description of what the workflow does, the required targets and variables, in addition to a contact particular person for help. Here’s what the workflow appears to be like like within the Trade simply earlier than set up.
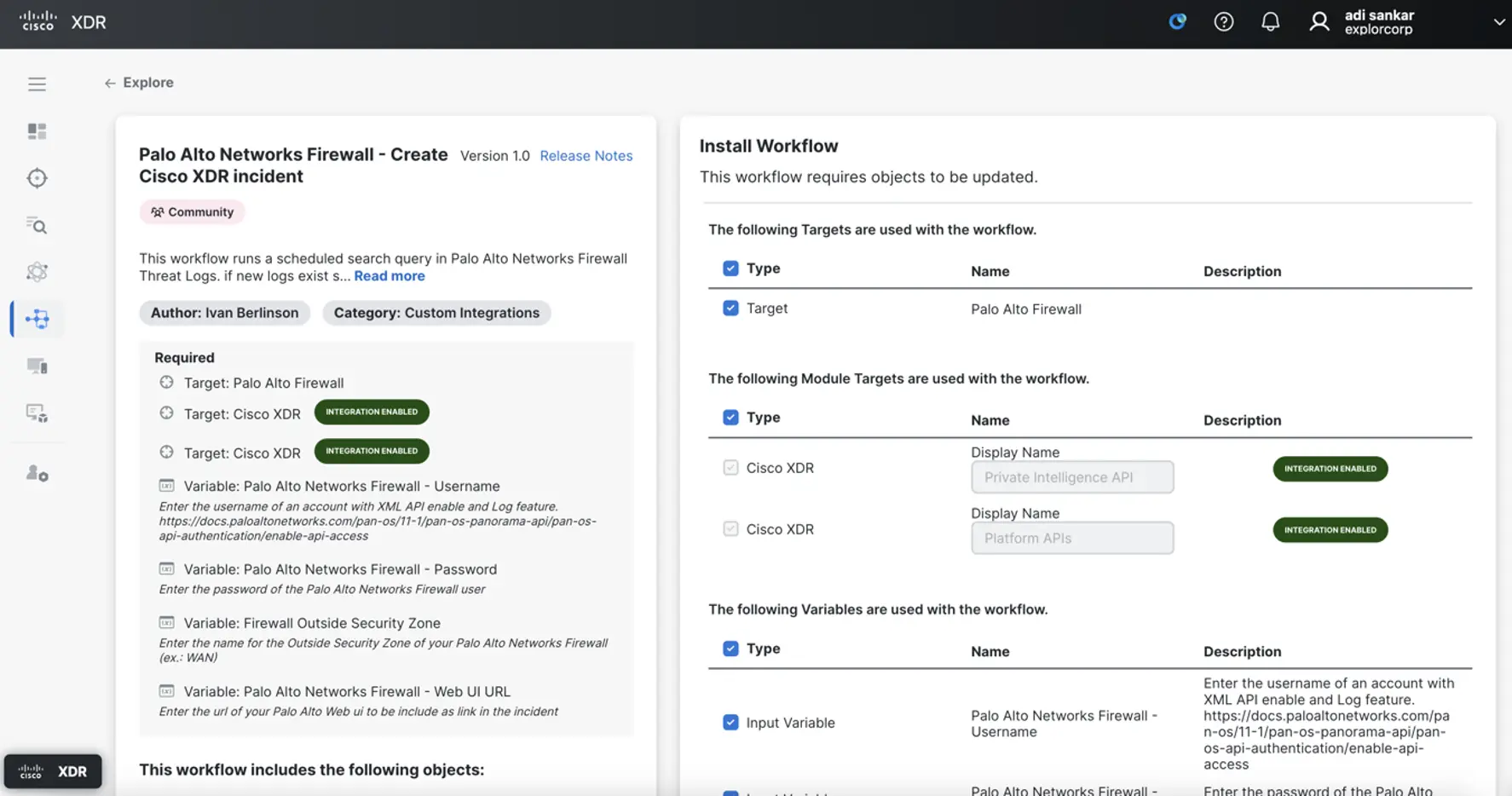
This workflow requires Automation distant, on-premises digital machine deployed over ESXi to make sure correct connectivity to the Palo Alto Panorama equipment. Shoutout to Matt Vander Horst who helped with the vCenter required to deploy the Automation distant equipment. The Trade prompts the person to supply values for the required variables and choose the suitable on-premises goal.
Then the workflow is put in and scheduled to run each quarter-hour by way of an automation rule.
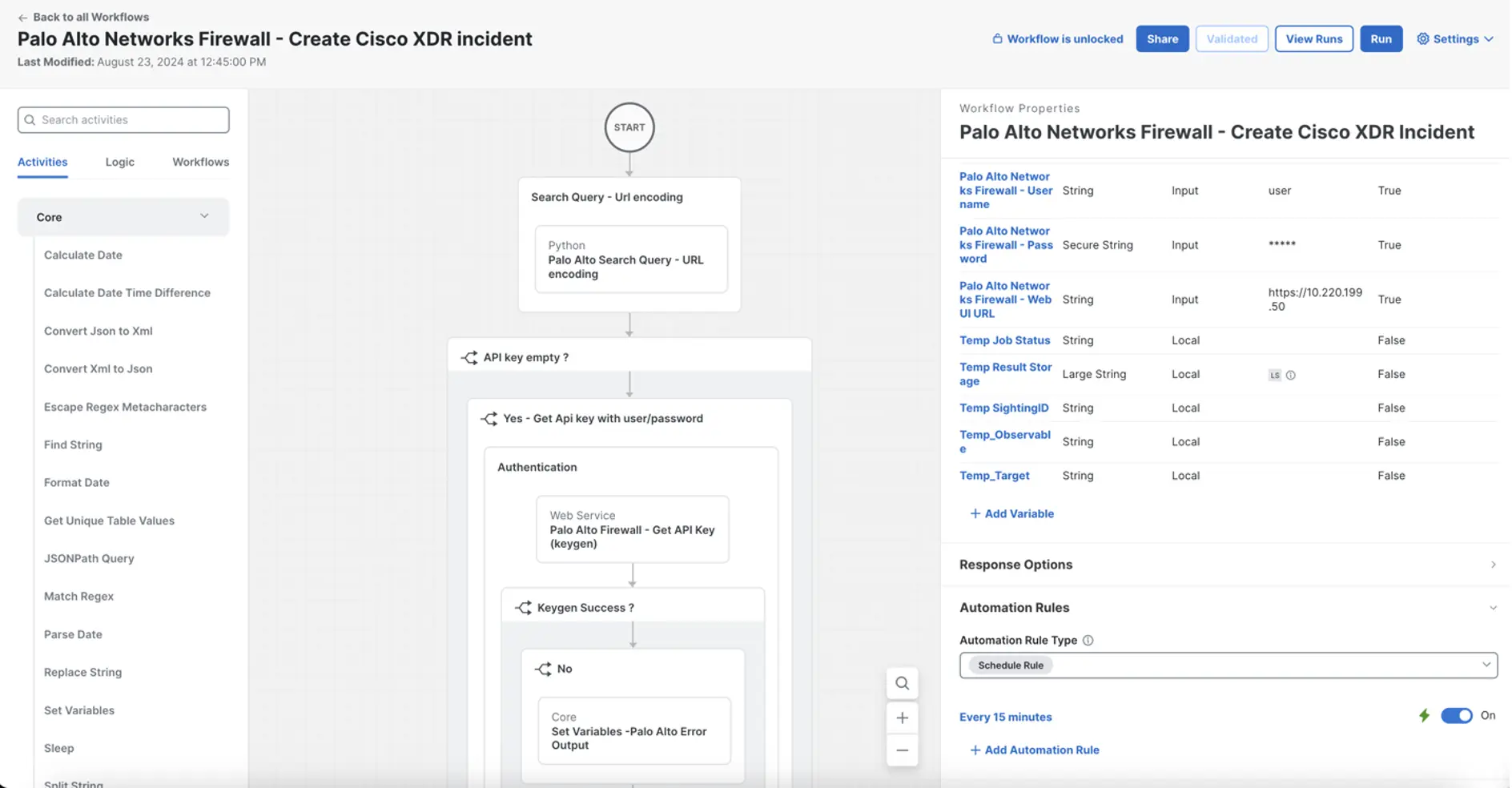
This workflow makes use of the PAN-OS XML API to question for risk logs at this path <?sort=log&log-type=risk&nlogs=50>. This kicks off a search job. As soon as the search job is finished, the workflow retrieves the outcomes and begins parsing the risk logs. A Cisco Risk Intelligence Mannequin (CTIM) sighting is created for every particular person risk log and grouped collectively by inside host IP. Subsequent, a CTIM indicator with the outline of the risk log and a relationship to the corresponding sighting are each created. Lastly, an incident bundle is created with the sighting, relationship and indicator entities and posted to the XDR API. The workflow has logic in-built to test for duplicate incidents and current indicators.

Here’s what one of many incidents that was created from this automation workflow appears to be like like in Cisco XDR. This gave us as analysts within the SOC a fantastic start line for an investigation.
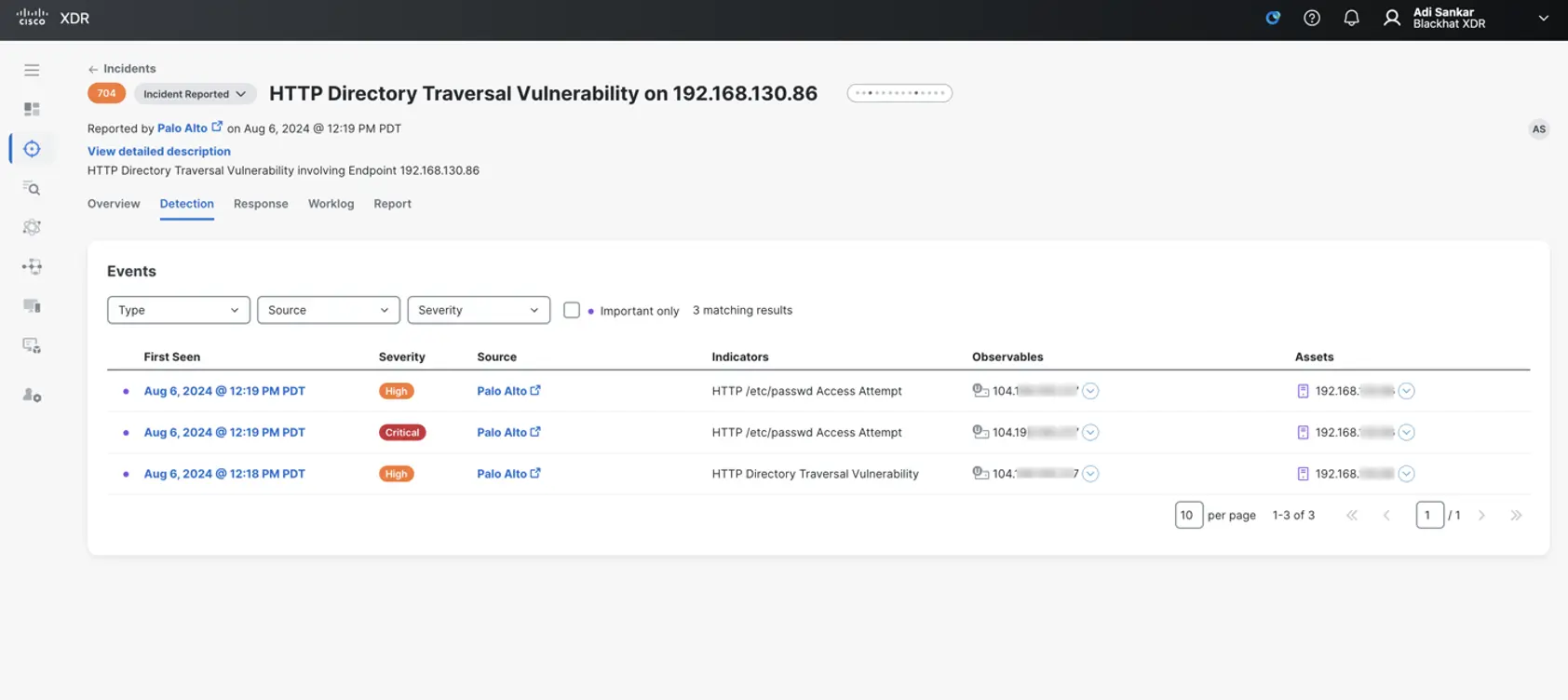
These Palo Alto Community risk logs point out a listing traversal assault that goals to entry information and directories which are saved outdoors the online root folder. PAN Firewall alerts on listing traversal and accessing </and many others/passwd> from supply IP 192.168.130.86 on common attendee Wi-Fi to vacation spot IP <104[.]198.XXX.2XX>, which resolves to < yXXXXis[.]get together>. This area is marked as suspicious by a number of risk intelligence sources and has a medium danger rating of 72 in Cisco Umbrella. The host then proceeded to obtain information from <file://var/run/secrets and techniques/> host with primary authentication within the HTTP POST header. This exercise was then correlated to related classroom exercise, however the host MAC handle was not seen in any school rooms.
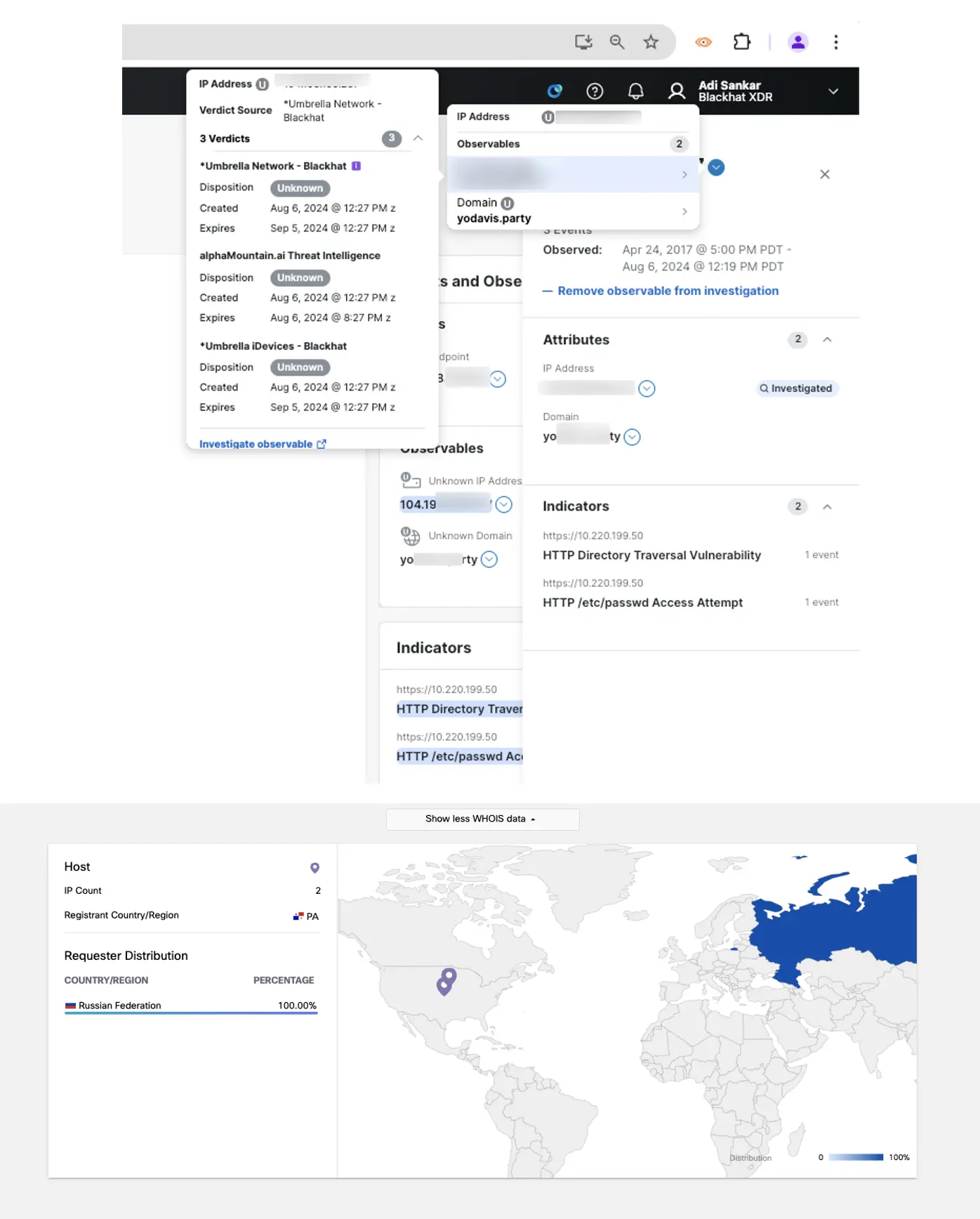
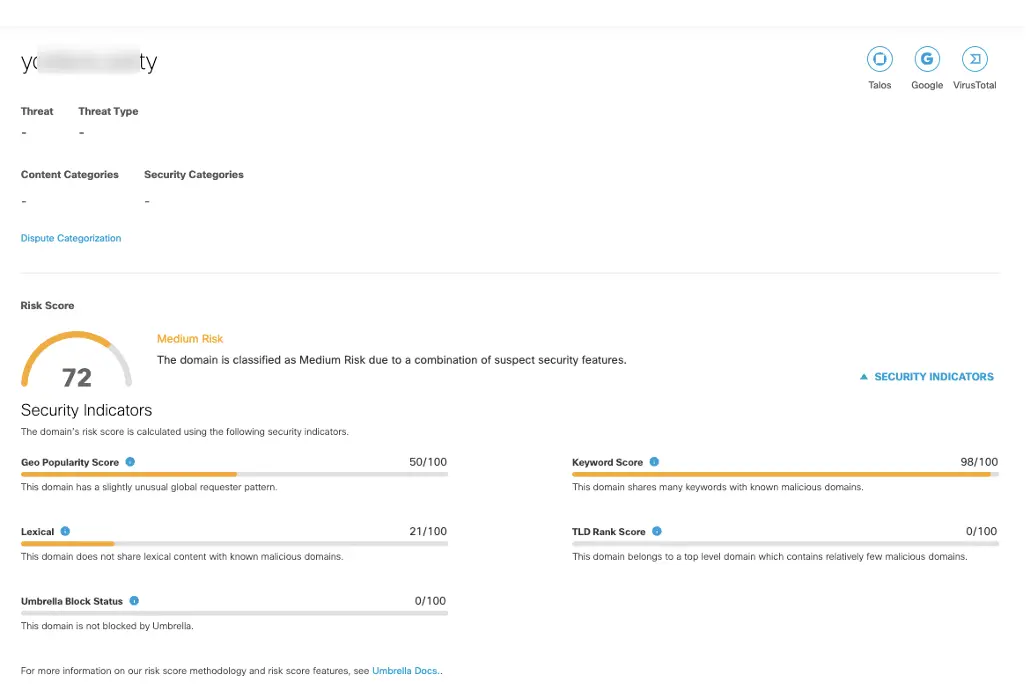
The vacation spot IP reveals unknown with XDR risk intelligence, however the area it resolves to appears to be suspicious and it’s hosted within the Russian Federation, as seen within the Umbrella console. Listed below are extra particulars offered by the Corelight workforce in our lively Risk Looking Slack chanel: HTTP POST exercise to the vacation spot in query reveals a primary authentication token that decodes to <admin:p034BHUSA43op> which does appear to be it’s getting used for Black Hat coaching because it says BHUSA within the password. Nonetheless, this supply host’s MAC handle was not seen in any school rooms, solely on the overall Wi-Fi.
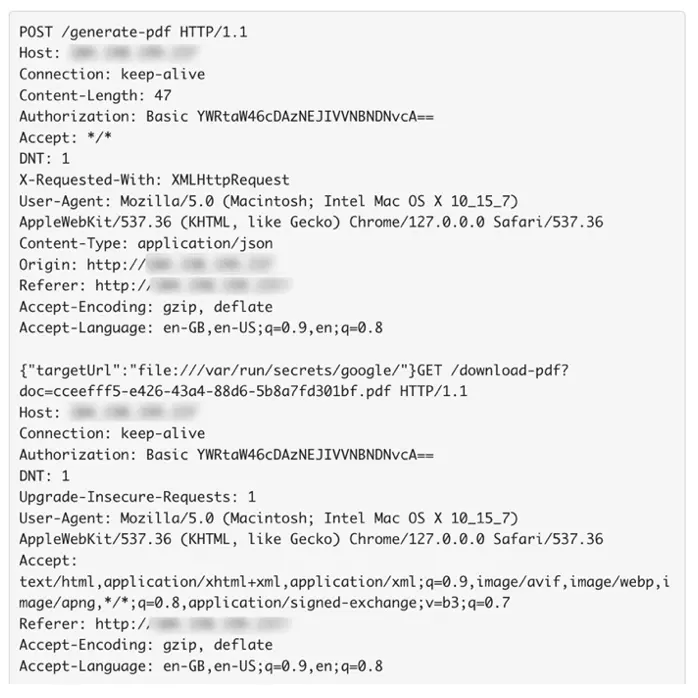
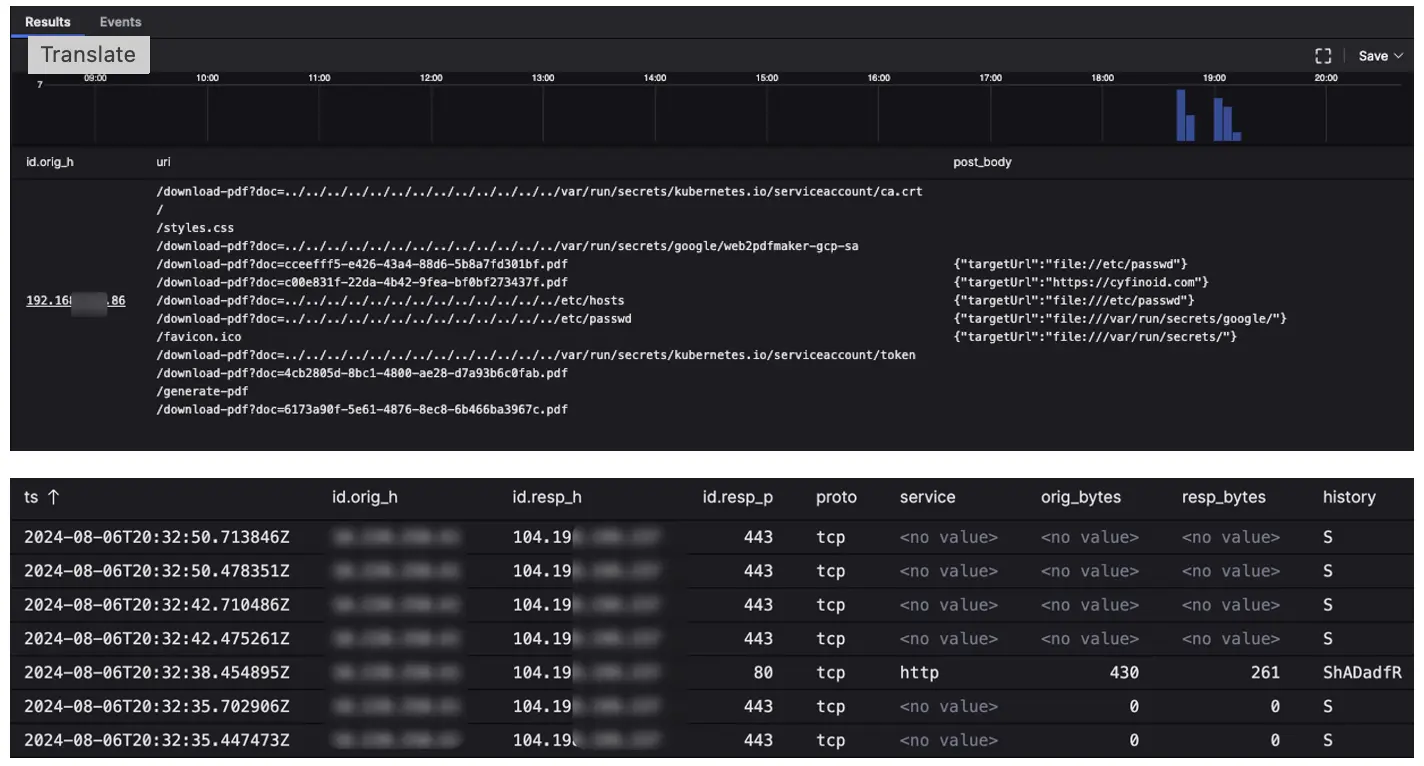
We did discover the host making related queries like <uri = /token$/ uri=/kubernetes/>, which had been seen within the Superior Infrastructure Hacking class, however it isn’t sufficient to attribute this exercise to a category. Anyhow, this habits usually shouldn’t be seen on the overall Wi-Fi. On this situation, we didn’t take any motion of blocking the vacation spot IP or forcing a captive portal for host IP because the Black Hat community goals to observe for assault and abuse, however not block malicious visitors.
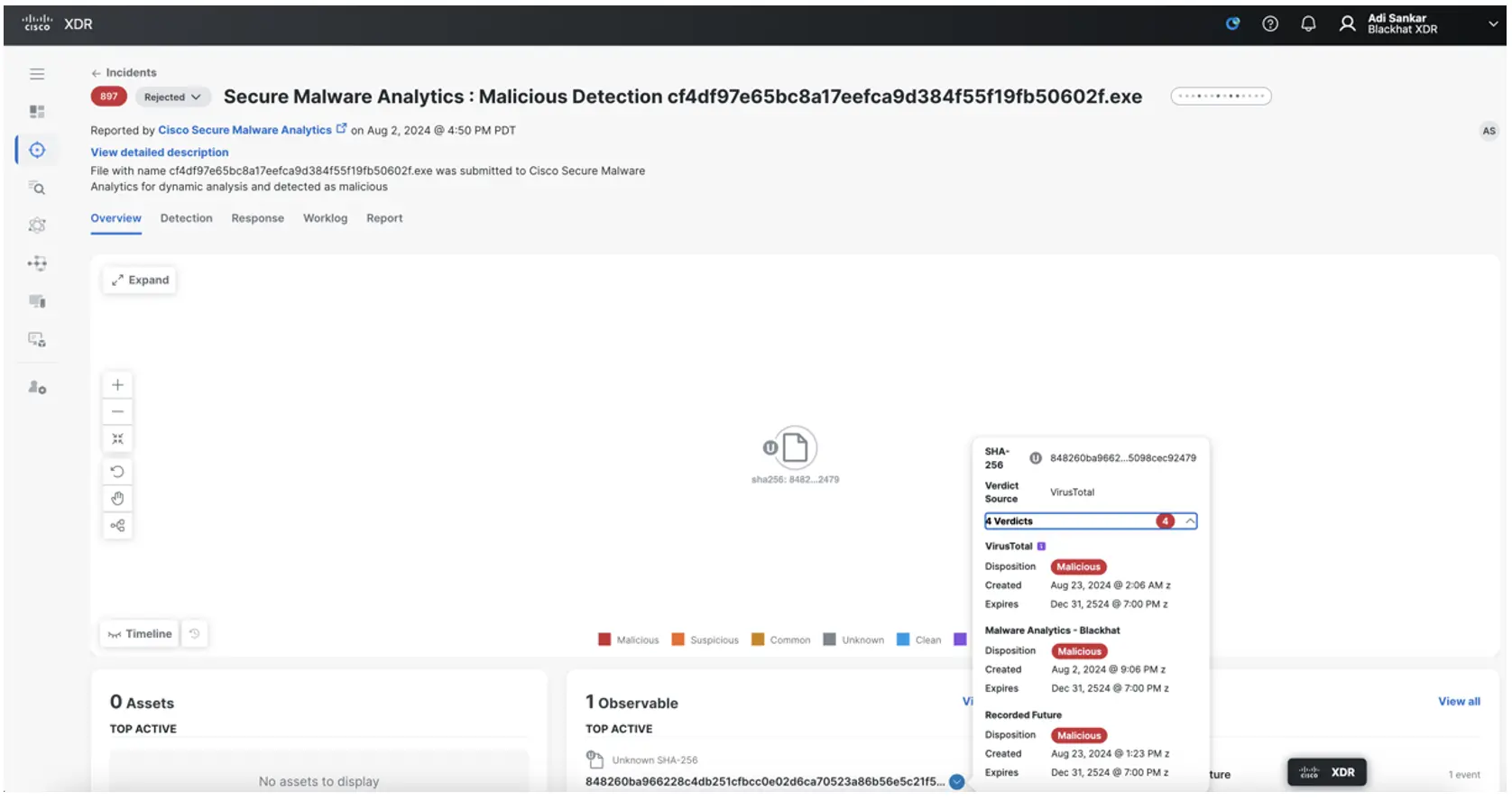
Ivan Berlison additionally offered one other workflow to supply an XDR Incident when a file is convicted in Cisco Safe Malware analytics. Corelight, in addition to NetWitness, carve information off the community and submit them to be detonated in Safe Malware Analytics. Here’s what the XDR incident appears to be like like when a file with a risk rating above 90 is seen:
We had an exquisite time innovating and investigating at Black Hat USA 2024! The XDR automation trade was an enormous assist in including extra automation capabilities with very minimal customized work. Take a look at AJ Shipley’s weblog on how utilizing Cisco XDR at Black Hat has accelerated our open ecosystem. We’ll be again once more subsequent yr, so lengthy Black Hat!
Splunk Assault Analyzer (SAA)
By: Ryan MacLennan
Splunk Assault Analyzer (SAA) is a brand new addition to our deployment. As chances are you’ll know, Cisco acquired Splunk this yr. Due to this new acquisition we labored with our counterparts in Splunk to get their SAA product provisioned for our use at Black Hat. SAA is a file and URL evaluation platform much like Safe Malware Analytics. SAA makes use of a classy set of standards to find out which engine could be greatest suited to evaluation — like internet analyzer, static file evaluation, electronic mail analyzer, signature engines and/or the sandbox. Whereas the product is able to dynamic and static evaluation, we selected to do solely static evaluation for our use at Black Hat.
What is actually highly effective concerning the evaluation of SAA is its assault chain following functionality: The power to intelligently decide how a human would click on on objects in a webpage. It’s going to comply with hyperlinks, obtain information and analyze extra indicators from community connections, identified malicious information, an unknown malicious file that’s analyzed on the fly, phishing domains and extra. It’s going to comply with a logical circulation like a human to find out the trail to compromise. This was fascinating to see in our surroundings because it confirmed the trail from a file, the hyperlinks present in it, to completely different web sites, and every step of the trail had a screenshot for us to comply with alongside.
For instance, now we have a PDF that was submitted to SAA. It discovered hyperlinks within the file and adopted them to see if they’d result in one thing malicious. I’ve blocked out a lot of the URLs, however we will see the way it went by means of the PDF knowledge and clicked on the hyperlinks to search out out the place it could go.
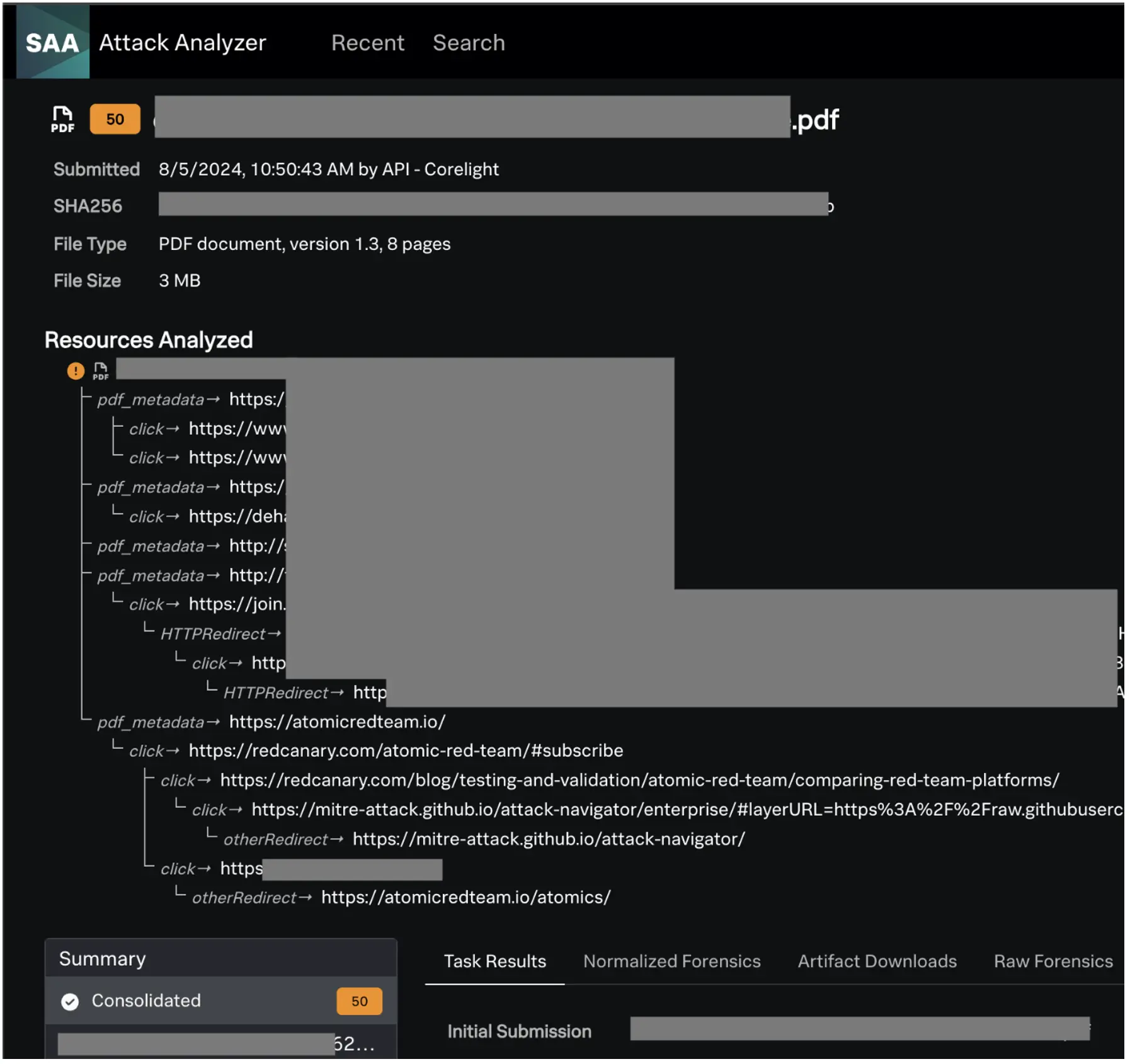
After SAA did its factor, we may have a look at the file in query and the screenshots that it took. We discovered that this file was the information utilized in a coaching room and every hyperlink was a reference to an article, a coaching useful resource (self-hosted and official), or different informational assets a pupil might have.
We had been in a position so as to add this integration with the assistance of our accomplice Corelight. We talked to them on day one and so they had been excited to get a brand new integration developed with SAA. A number of hours later, we had an integration with them. This was a tremendous instance of how all of us come collectively to make the NOC higher at Black Hat yearly.
Umbrella DNS
By: Christian Clasen and Justin Murphy
If in case you have learn the earlier Black Hat NOC/SOC reviews, you already know that in 2023, we made a change to the DNS design. In prior conferences, we assigned inside forwarders to purchasers by way of DHCP, however didn’t pressure their use. Primarily, attendees may use any DNS resolvers they selected, and we didn’t intervene. The change we carried out was to start forcibly redirecting DNS visitors to the on-premises DNS forwarders. You may see within the statistics above that this transformation prompted a major soar in queries processed by Cisco Umbrella — from 54.4 million to 79.3 million.
The steep enhance in question rely was not sudden. What was sudden, nonetheless, was a lower in question rely between 2023 and 2024. Whereas we don’t know the exact reason for this drop, we do have some theories and methods we will take a look at them going ahead.
One potential rationalization is the prevalence of encrypted DNS protocols. Lately, the trade has turned its consideration to the privateness, integrity and authenticity issues inherent within the plain-text DNS protocol. To unravel a few of these points, “last-mile” encryption has change into a favourite of OS and browser distributors. DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) are solely a few the most well-liked methods to encrypt DNS between the consumer and the recursive resolver.
Detecting all encrypted DNS could be tough and counting the queries not possible. It’s because TCP is the chosen transport for DoH and DoT, and this enables the consumer to pipeline a number of queries over one long-lived TCP and TLS session. However what we will usually discover are the “bootstrap” plain-text DNS queries that allow to consumer to search out the encrypted DNS server. By working a report in Umbrella for the class “DoH and DoT”, we will get a deal with on the most well-liked of those providers:

The entry for <dns.google> is more than likely indicative of Android cellular units who use this DoT resolver by default. The rely of queries for that specific service is more likely to be larger as a result of the classes on these units are identified to be short-lived if queries usually are not frequent sufficient.
On this report, we additionally see “canary” domains corresponding to <canary.masks.icloud.com> and <use-application-dns.web>. The latter area is utilized by Firefox to detect when it ought to fall again to unencrypted DNS on the community. Extra particulars on how Umbrella interacts with these is written up within the Umbrella help article for internet browsers and DoH default.
Going ahead, we are going to observe the statistics of those protocols on the convention networks and see what different data we will collect utilizing the total packet seize capabilities of our companions and the risk searching capabilities of Cisco XDR. You may anticipate this subject to be expanded on within the subsequent convention report.
One of many major causes to not less than monitor DNS is to know traits and the way the community at Black Hat is getting used from a excessive degree. There are numerous insights that may be gained from forcing DNS by means of a centralized service with intelligence. DNS queries exist for locations that host every thing from Malware, Crypto Mining and Phishing to content material classes like Social Media, Finance and Unlawful Actions. Moreover, these domains could be categorized into particular purposes as properly. With the App Discovery report in Umbrella, these domains are grouped by software, figuring out the potential use of 1000’s of purposes. This might be internet apps or different desktop/cellular apps.
As all the time, we proceed to see an increase in app utilization at Black Hat:
- BHUSA 2019: ~3,600
- BHUSA 2021: ~2,600
- BHUSA 2022: ~6,300
- BHUSA 2023: ~7,500
- BHUSA 2024: ~9,300
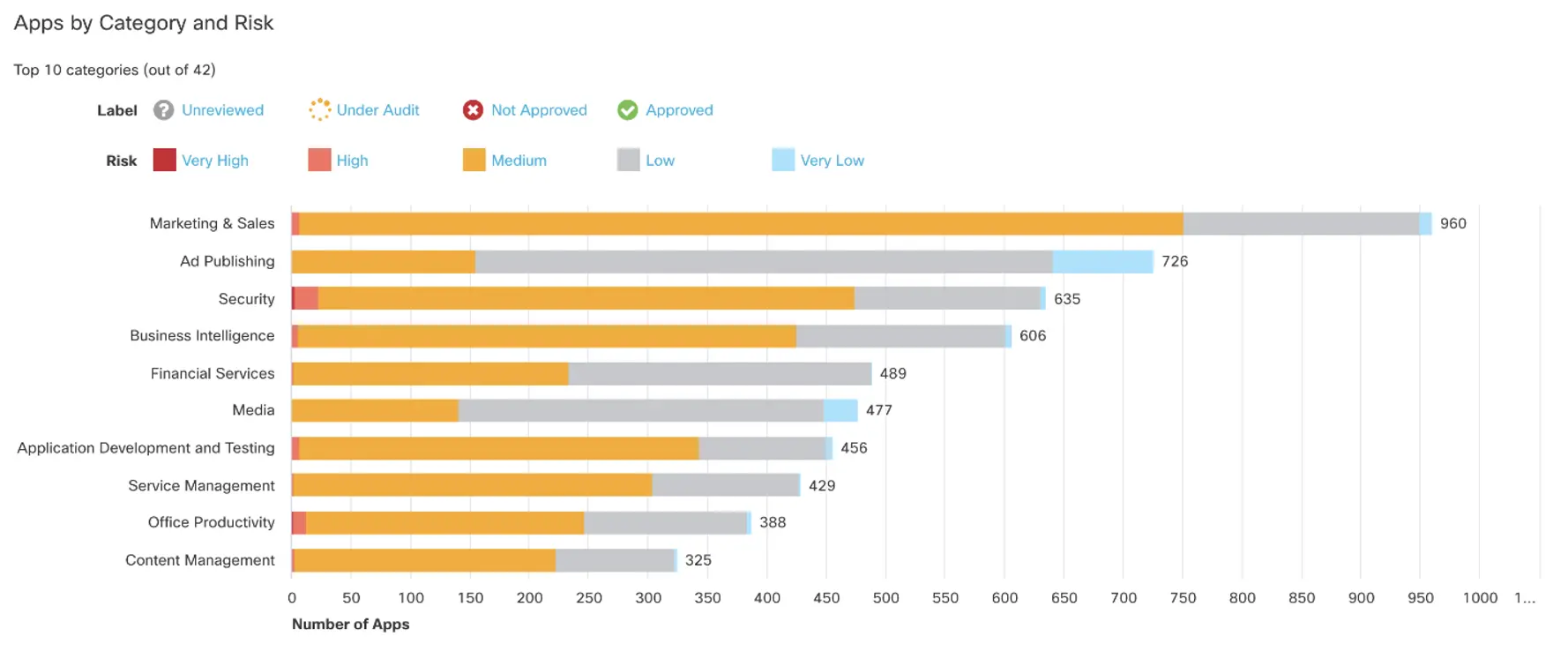
This yr there was one stand out Software Class that has been rising in recognition: Generative AI. It’s going to probably be no shock that there are extra attendees and their instruments utilizing Generative AI. We’ve gone from seeing it as a footnote in logs to reporting it at RSAC 2024, as we noticed 80 completely different Generative AI instruments getting used.
Evaluate this to Black Hat 2024, just some months later, the place the entire quantity has jumped to 194.
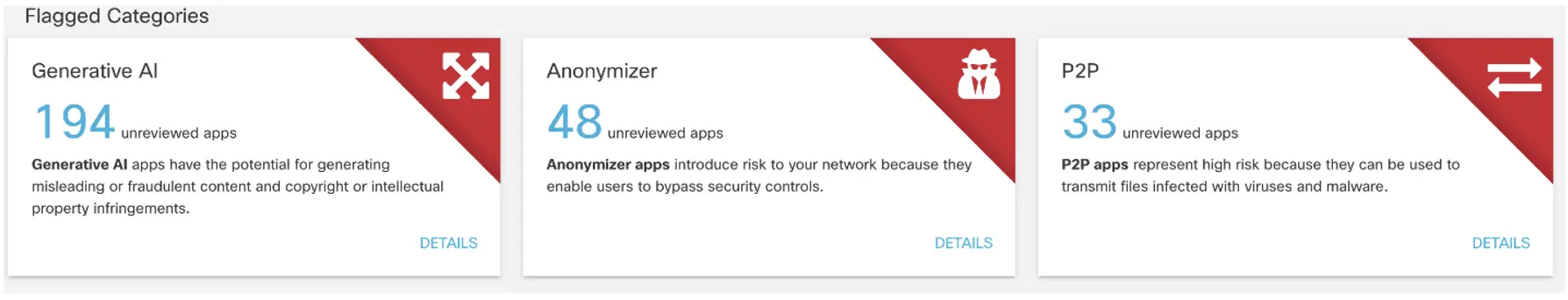
This doesn’t look like only a distinction in conferences, however fairly a rising pattern and acceptance of those instruments.
Community Assurance
By: Adam Kilgore, Shimei Cridlig, Shannon Wellington and Justin Murphy
The ThousandEyes deployment launched at Black Hat USA 2023 one yr in the past. At that convention, we spent many lengthy shifts growing the configurations, design, and procedures that fashioned the premise for our convention protection. The deployment was additional improved and streamlined at Black Hat London and Black Hat Asia. At this yr’s Black Hat USA 2024, we had been able to increase our protection considerably whereas persevering with to refine our procedures.
New {hardware}
We added 20 Orange Pi units at Black Hat 2024, along with the 8 Raspberry Pi units we deployed in 2023. We’re nonetheless properly in need of the proverbial thousand eyes, however 28 is much more than 8. We deployed our new fleet of Orange Pi units to observe the wi-fi community, whereas the previous Raspberry Pi units had been used for wired monitoring of Registration, the NOC and core community units.
Orange Pi configuration

Mike Spicer put in plenty of time to develop new configuration and deployment procedures for the Orange Pi units earlier than the convention. We had been in a position to make use of a script and a small native community to configure every Orange Pi with a particular SSID and PSK. As soon as the Pi units had been configured and the goal entry factors had been deployed, every Pi was walked to its goal coaching room the place it could robotically connect with the entry level (AP) on bootup and start working its scheduled monitoring assessments.
Even with the scripting and automation, the configuration stage nonetheless resulted in a mass of wires (pictured above). Deploying the Pi units resulted in additional strolling than the common attendee would expertise in a convention (not pictured).
Expanded wi-fi protection

With the extra brokers, we had been capable of deploy to extra Black Hat coaching rooms. The expanded visibility allowed us to catch extra issues earlier than the coaching rooms went dwell, together with a misconfigured PSK, an SSID that wasn’t broadcasting and an SSID that broadcast however didn’t have web connectivity. We’d like to have an agent for every coaching room for full visibility and validation heading into the convention, however we’re pleased with what we caught and the extra confidence the brokers offered heading into the coaching days.
Because the convention shifted from trainings to the briefing days, we shifted our protection from the biggest coaching classes to massive briefing rooms and heavy-traffic areas like the doorway and Enterprise Corridor. Whereas we nonetheless needed to make powerful strategic selections about what to cowl and what to not cowl, we had been nonetheless capable of unfold brokers throughout every ground for common visibility.
Troubleshooting
Our experiences over the previous three conferences had produced well-established troubleshooting procedures and paperwork for the Raspberry Pi units, however the Orange Pi devicess introduced recent challenges. We had round 25% of our deployed Orange Pi units require troubleshooting through the first 24 hours after deployment, a regarding price. Log evaluation revealed the wi-fi NIC changing into disconnected and the USB getting into a disconnect loop (the wi-fi NIC is related by way of USB on the Orange Pi units). The issues with the wi-fi NIC and USB result in a recurring ThousandEyes agent core information — a tough set of issues.
Nonetheless, these points turned out to be remoted fairly than widespread, and by the top of the convention we had a full wi-fi deployment that was staying up all day and in a single day as properly. For what turned out to be remoted wi-fi issues, we developed troubleshooting procedures and documentation.
Automated ticketing
A brand new ticketing system was rolled out at this convention that might create tickets in Slack primarily based on ThousandEyes knowledge or reported points. Under is a ticket created primarily based on TE alerts for a particular convention room through the first morning of briefings.
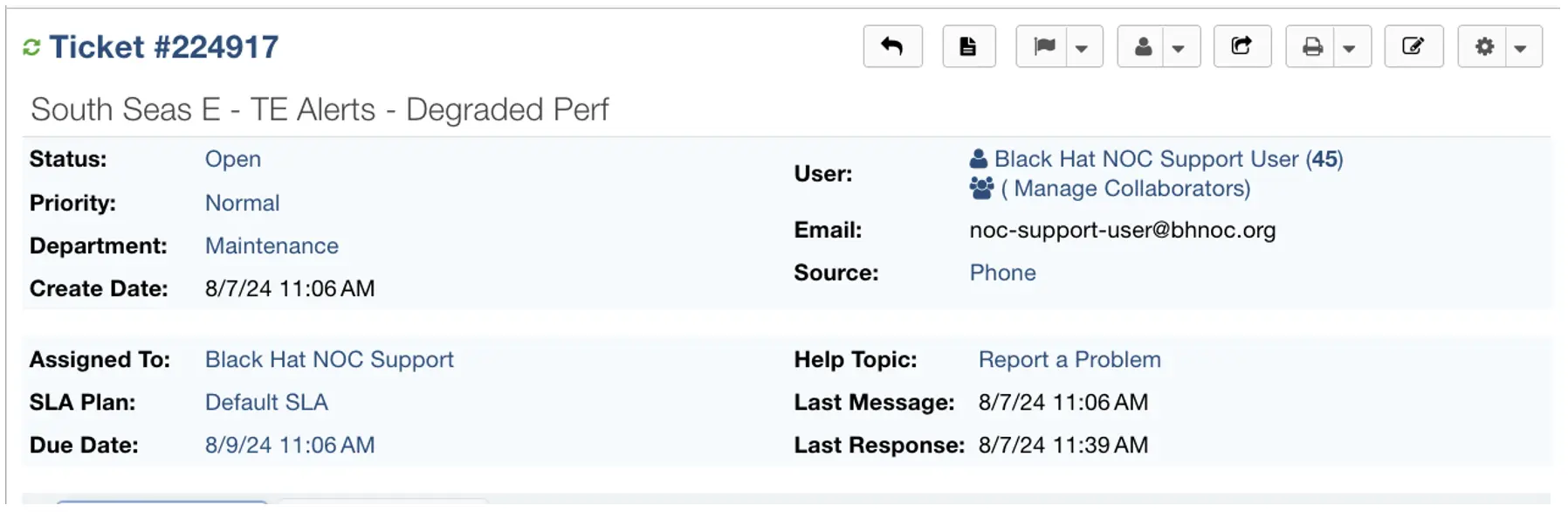
The dashboards in ThousandEyes allowed us to supply fast visible data that confirmed which convention rooms had been experiencing the worst latency, alongside a comparability of latency throughout reporting rooms.
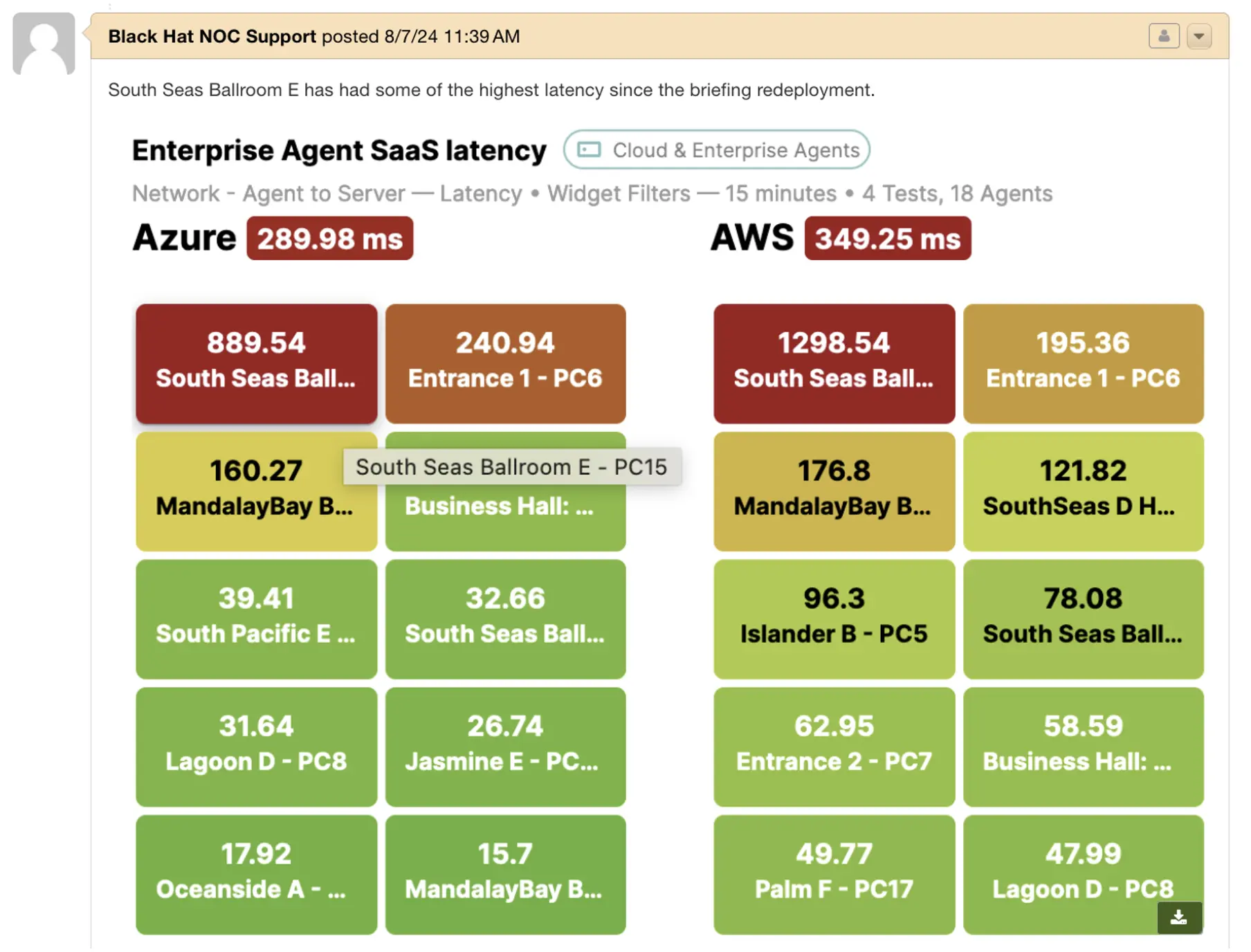
The automated reviews behind every dashboard entry offered extra granular data, together with visitors path and the latency alongside every leg within the visitors path.
The brand new ticketing system allowed screenshots like those above to be aggregated within the ticket for workforce communication and report retaining.
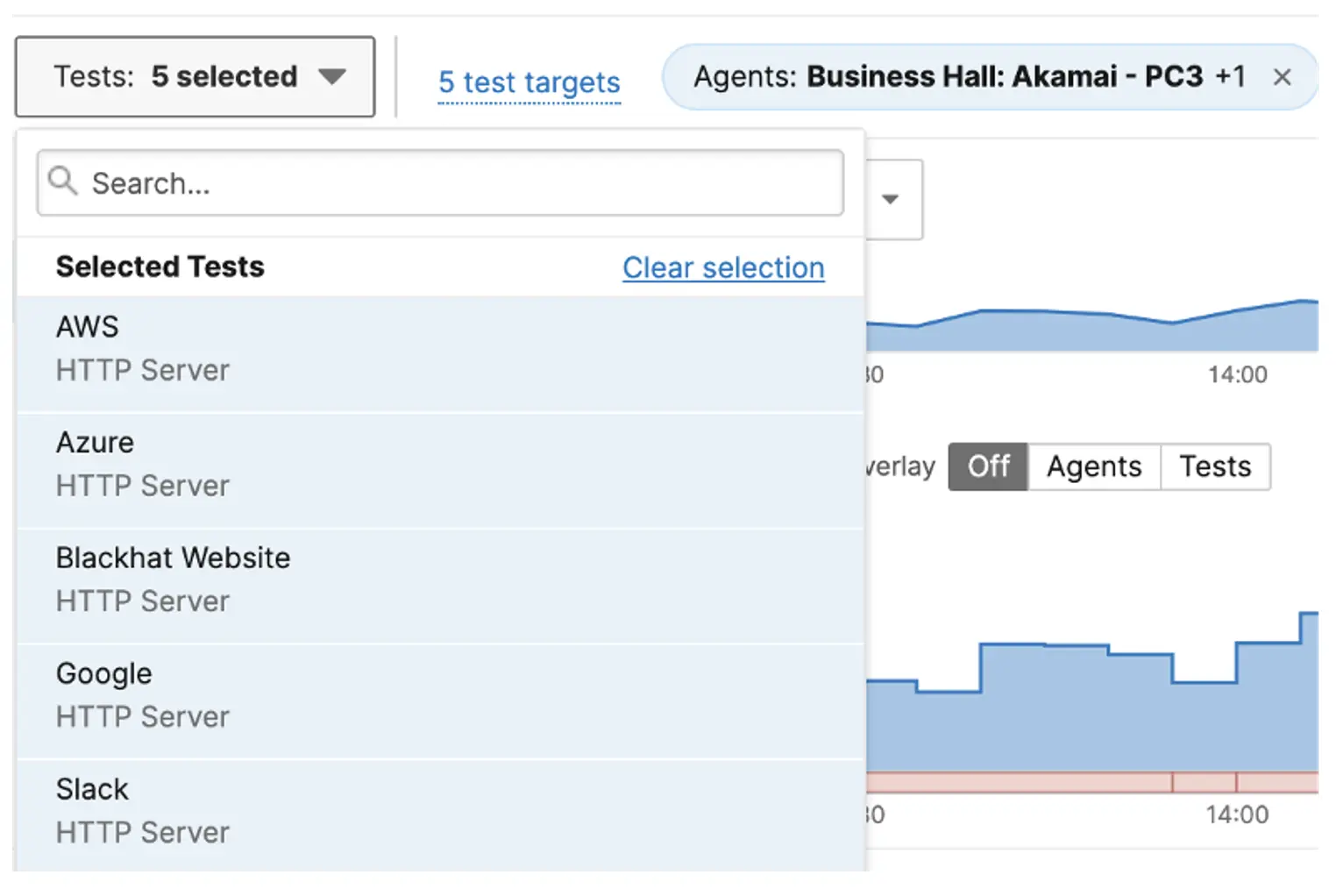
Troubleshooting WorkflowOn 08/06/2024 at 15:00, we noticed excessive latency to our Inner Umbrella DNS take a look at from the South Seas D Hallway and Enterprise Corridor Brokers. Word that the hyperlinks to the investigation views are offered as hyperlinks.
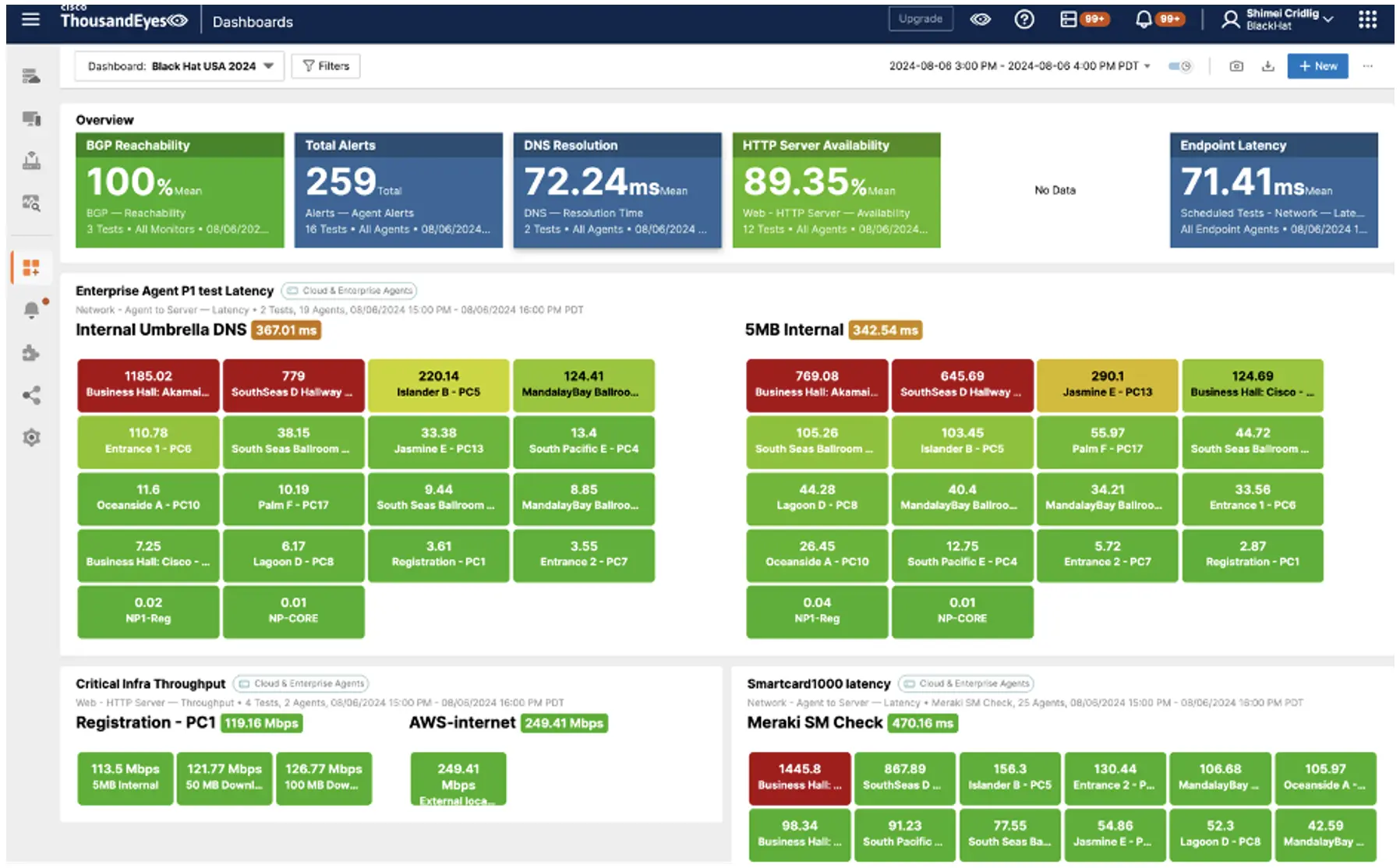
To slender down the view, we used a dashboard filter to deal with the 2 Brokers.
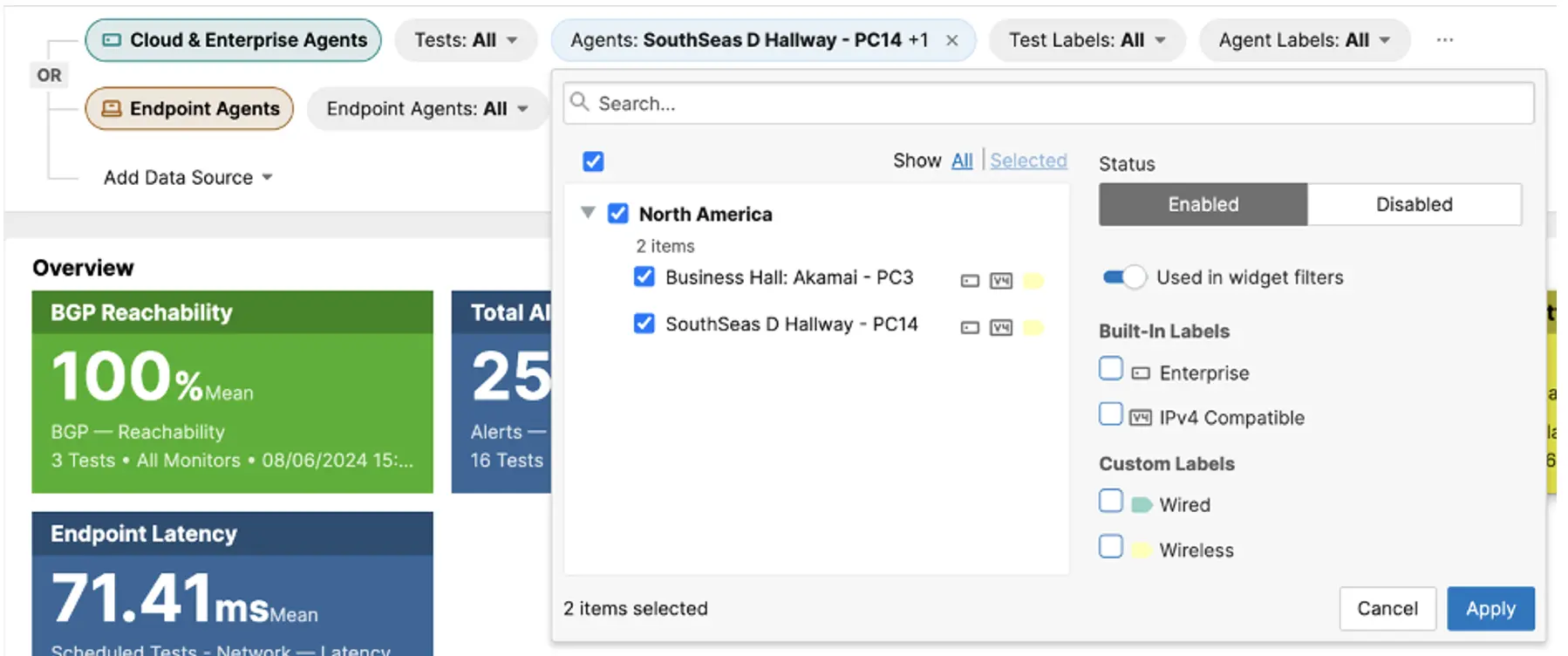
This confirmed the excessive latency noticed by the 2 Brokers prolonged throughout a number of assessments.

From right here, we drilled down on every take a look at to test the person take a look at outcomes.
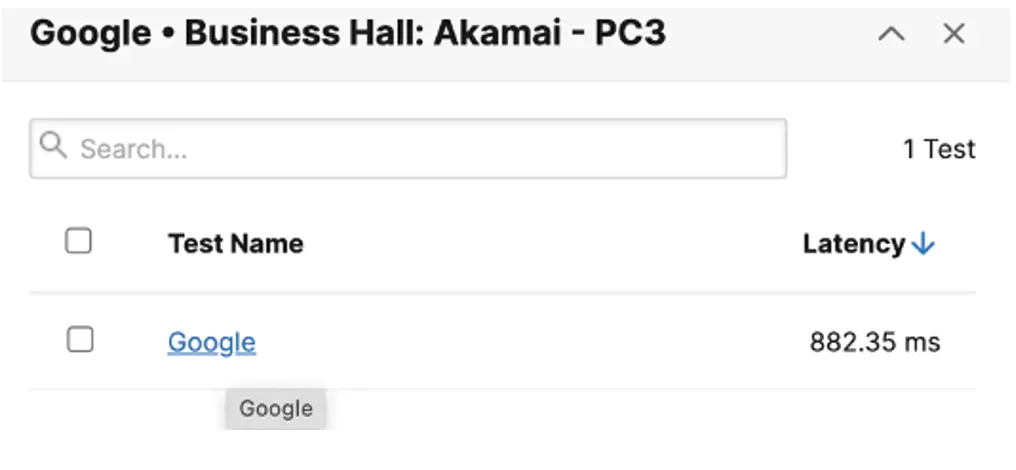
Inside this view, we chosen a number of assessments working on each Brokers and in contrast the outcomes.
We noticed that there was a latency spike reported by each Brokers.
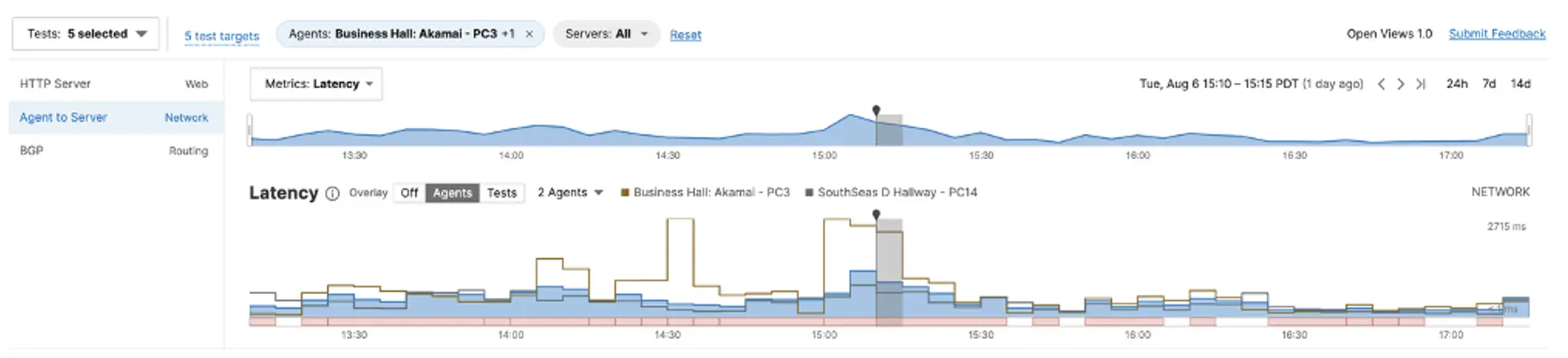
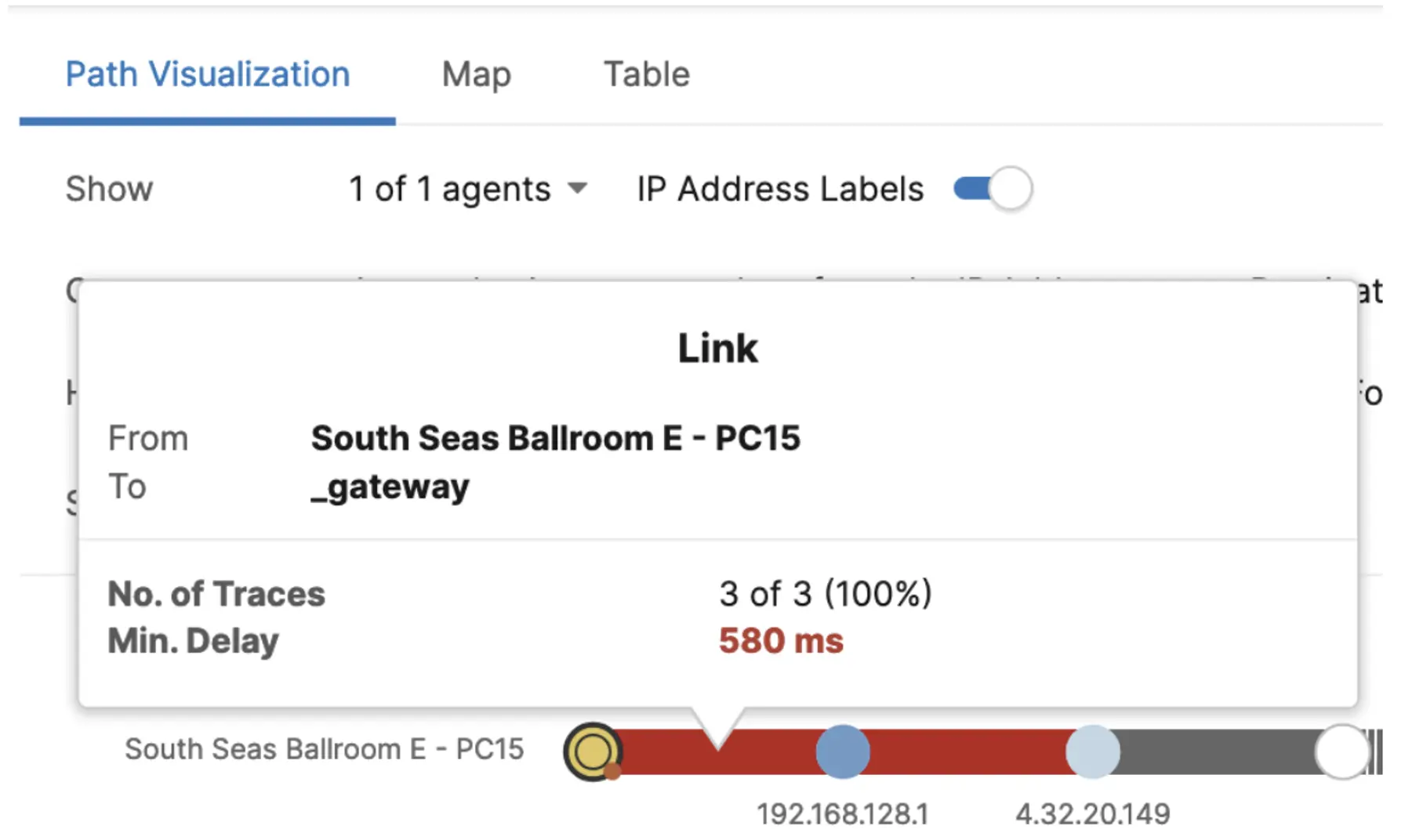
To know the reason for the excessive latency, we drilled all the way down to Path Visualization.
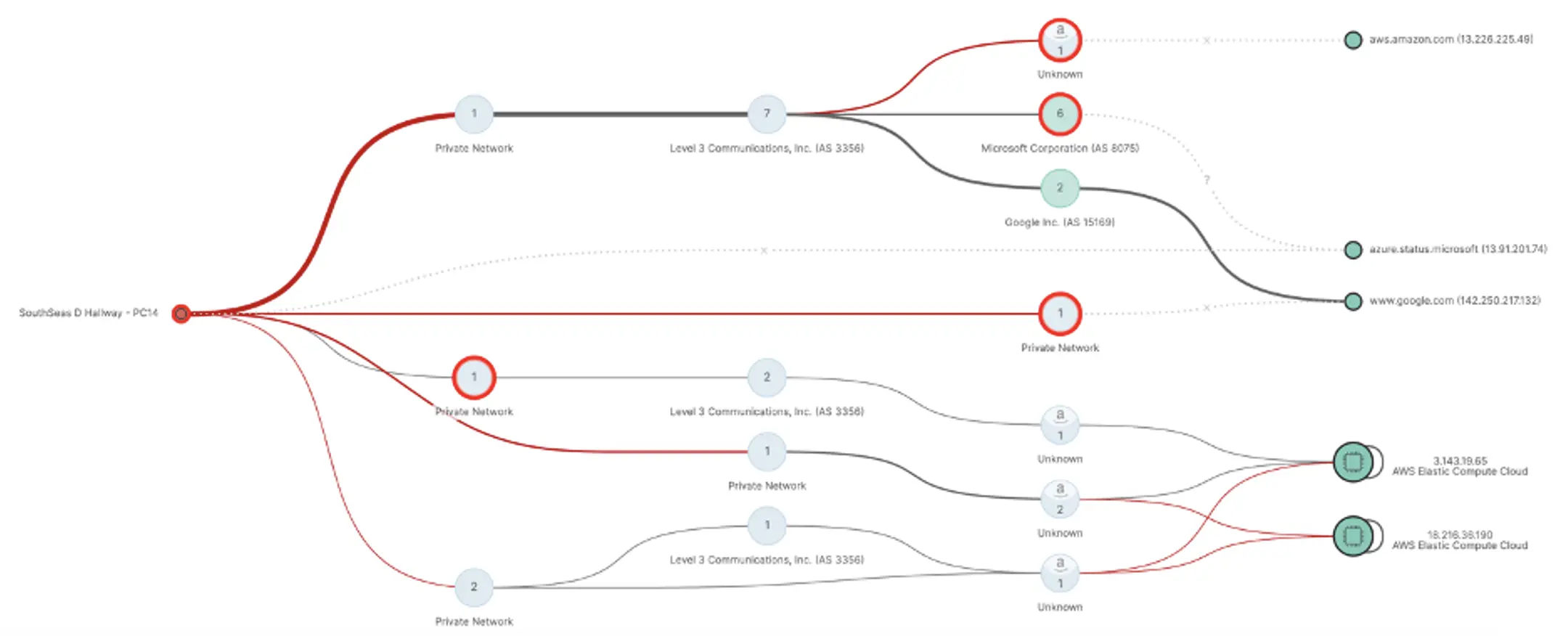
We seen the excessive hyperlink delay between the Agent to its gateway. This means a difficulty both between the consumer and AP or between the AP and the server room with the router.
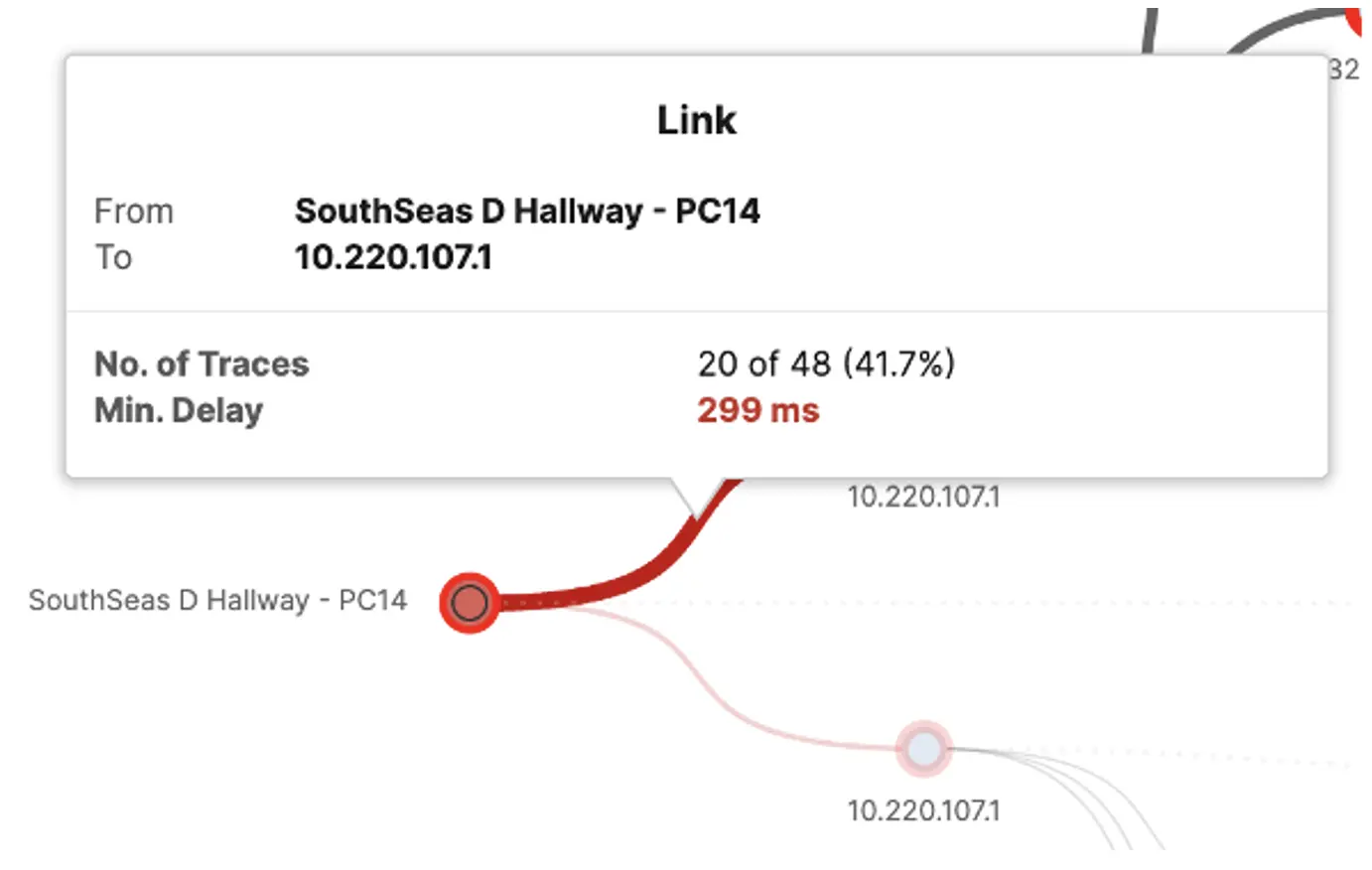
To substantiate the reason for the latency, we visited South Seas D. We ran extra assessments to substantiate that the connection expertise match with the outcomes reported by the Agent. Reviewing the room and topology diagrams additional, we discovered that the AP overlaying South Seas D was positioned in an adjoining room, and was broadcasting two SSIDs — one for the room it was positioned in, and the opposite for South Seas D. The mix of the AP placement, the AP servicing two rooms, and the attendee quantity in South Seas D mixed to supply the latency noticed by the Agent. These findings had been shared with the wi-fi workforce.
Cellular machine administration at Black Hat: The position of Meraki Methods Supervisor
By: Dalton Ross
The Black Hat cybersecurity occasion in Las Vegas is famend for its cutting-edge know-how and seamless attendee expertise. A important part of this success lies in efficient cellular machine administration (MDM). Since Black Hat USA 2021, we leveraged Cisco Meraki Methods Supervisor (SM) to deal with a wide range of duties essential to the occasion’s operations. Under is an in depth have a look at how the Meraki SM was deployed and the challenges confronted alongside the best way.
Important roles of cellular units at Black Hat
Cellular units had been pivotal in a number of key areas:
- Registration Kiosk iPad Units (~50 Units): Used at registration kiosks to streamline the attendee check-in course of, the place attendees scan a QR code for fast badge printing
- Session Scanning iPad Units (~75 Units): Deployed throughout Black Hat classes to scan registered attendees into every session
- Lead Retrieval Units (~800 Units): A considerable variety of units had been utilized on the present ground cubicles to swiftly gather sales space customer contact knowledge

Deliberate deployment for Meraki Methods Supervisor
To make sure a easy deployment, our technique included a number of key steps:
- Pre-State with Apple Automated Machine Enrollment (ADE): Earlier than cargo to the occasion location, all units had been pre-staged utilizing ADE. This allowed units to be configured with a identified SSID for sooner deployment on website.
- Segregated Delivery: Units had been to be shipped in three distinct groupings, every akin to one of many roles. This aimed to facilitate swift deployment upon arrival.
- Dashboard Script for Position Affiliation: A customized dashboard script was ready to leverage the Meraki Dashboard API and simply affiliate enrolled units with their respective roles.
- Automated Configuration Obtain: As soon as powered up, units had been anticipated to robotically obtain any obligatory configurations or apps associated to their position, making them prepared for instant deployment.
- Well being Monitoring with Cisco ThousandEyes: ThousandEyes brokers had been to be deployed all through the venue to log SM well being at completely different occasion places.
- Publish-Occasion Manufacturing facility Reset: After the occasion, all units had been to be manufacturing unit erased earlier than being returned.

Challenges and workarounds
As in life, challenges arose that required fast considering and adaptation:
- Software Listing Modifications: A final-minute change to the applying listing for session scanning units was required. Though we initially deliberate to have all configurations prepared beforehand, this sudden change was effectively managed utilizing the Methods Supervisor with just some clicks.
- ThousandEyes Agent Limitations: Since ThousandEyes brokers had been beta SM purchasers, they couldn’t precisely collect connectivity knowledge. This was an anticipated habits, nevertheless it posed a problem for efficient monitoring. To beat this, NOC members from Cisco ThousandEyes and Cisco Meraki collaborated to hack collectively a proof of idea. Via laborious work and a number of other iterations, we configured the ThousandEyes brokers to simulate machine check-in visitors, mimicking legitimate SM purchasers.

Deploying Meraki Methods Supervisor at Black Hat was an intricate however rewarding endeavor. Regardless of dealing with challenges, our workforce demonstrated agility and innovation, making certain the occasion’s operations ran easily. The expertise underscored the significance of flexibility and fast downside fixing in managing large-scale occasions.
By leveraging superior MDM options like Meraki Methods Supervisor, we had been capable of present a seamless expertise for attendees and exhibitors alike, showcasing the ability of know-how in occasion administration.
We’re pleased with the collaboration of the Cisco workforce and the NOC companions. Black Hat Europe can be December 9-12, 2024 on the London eXcel Centre.

Acknowledgements
Thanks to the Cisco NOC workforce:
- Cisco Safe: Christian Clasen, Matt Vander Horst, Aditya Sankar, Ben Greenbaum, Ryan Maclennan, Adam Kilgore, Shimei Cridlig, Shannon Wellington and Justin Murphy, with distant help by Jessica (Bair) Oppenheimer
- Meraki Methods Supervisor: Dalton Ross, with distant help by Paul Fidler and Connor Laughlin. Search for their report on The Meraki Weblog.
Additionally, to our NOC companions:
- NetWitness (particularly Alessandro Zatti)
- Palo Alto Networks (particularly Jason Reverri and James Holland)
- Corelight (particularly Dustin Lee)
- Arista (particularly Jonathan Smith)
- Lumen and all the Black Hat/Informa Tech workers (particularly Grifter ‘Neil Wyler,’ Bart Stump, Steve Fink, James Pope, Mike Spicer, Sandy Wenzel, Heather Williams, Jess Stafford and Steve Oldenbourg)
About Black Hat
Black Hat is the cybersecurity trade’s most established and in-depth safety occasion collection. Based in 1997, these annual, multi-day occasions present attendees with the most recent in cybersecurity analysis, growth, and traits. Pushed by the wants of the group, Black Hat occasions showcase content material immediately from the group by means of Briefings shows, Trainings programs, Summits, and extra. Because the occasion collection the place all profession ranges and educational disciplines convene to collaborate, community, and focus on the cybersecurity subjects that matter most to them, attendees can discover Black Hat occasions in america, Canada, Europe, Center East and Africa and Asia.
Share:
